(3) Attacks that paralyze the operation of the Web server system. This is a form of DOS attack aimed at our Web server system and this is also a fairly common form of attack on the network aimed at Web server systems.
(4) Impersonating users to make fake transactions.
(5) Eavesdropping on communications.
7.4.3. Information security for commercial websites
Since 1995, when websites such as amazon.com (known as the king of e-commerce), ebay.com (the world's leading electronic auction site), Yahoo! portal established in 1998, etc. began operating, companies and individuals doing business online have had to face new types of crimes (cybercrime or Internet technology crime) using many methods and tricks to attack or infringe on property, destroy websites, steal information, disrupt business website systems as well as take control of commercial servers.
Data from the new website security report published by CyStack shows that in the third quarter of 2019, the CyStack Attack Map system recorded up to
127,367 websites were attacked globally, a slight decrease compared to the same period in 2018. “Thus, every minute that passes, a website is hacked. When successfully attacking a website, hackers can perform many different damaging actions such as: stealing business data, changing the website interface (deface), inserting malicious code, redirecting users to phishing pages...”, CyStack experts analyzed.
Also in the website security report for the third quarter of 2019, the number of website attacks in Vietnam in the last 3 months increased by 113% compared to the same period last year (2,523 compared to 1,183). This number also puts Vietnam in 10th place on the list of countries with the most website attacks in the world. In which, the domain names .com, .vn and .net are attacked the most.
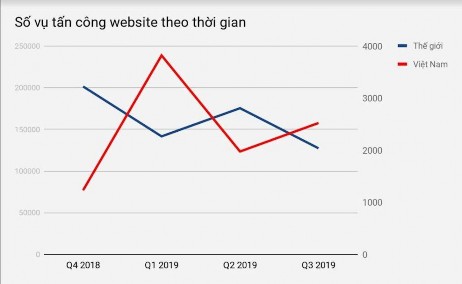
Figure 7.9. Number of website attacks over time
(According to CyStack Attack Map of CyStack Q3/2019)
The above attacks have caused great damage to the assets and reputation of online businesses. Most of the attacked e-commerce websites are giant electronic "supermarkets" that have been suspended, making it impossible for customers to access to buy goods, bid or conduct commercial transactions. The damage during the interruption will be difficult to determine in terms of material (how many transactions were suspended, how many customers did not access the website, how much the transaction value was, ...). In addition, the attack on leading e-commerce websites also affects customers' trust in the business, affecting the reputation of the business.
Table 7.1. Some attacks on famous websites around the world
Website name
Time and damage | |
Yahoo! | In 2014, Yahoo revealed that they had suffered an Internet attack that affected 500 million accounts and there was no need to argue much because not only were these accounts hacked, but these accounts were also used to continue to defraud the owners' relatives. Information such as names, dates of birth, and stolen phones caused a fever at that time. Despite Yahoo!'s assertion that this information leak would not affect bank accounts, Yahoo!'s users plummeted. Previously in 2012, the group of attackers “Peace” sold 200 million user information with passwords for $1900 on the Internet. The worst thing happened to Yahoo when they were attacked again, affecting 32 million accounts, the attackers used the same method as before, the attackers created malicious cookies on the Internet and logged in without Yahoo password. The sad ending when Yahoo! From a billion-dollar company had to sell itself for $4.5 million in 2017 to Verizon. In December 2018, Yahoo continued to admit that in the past they had lost all 3 billion accounts to Hackers. This can be considered the biggest attack in the history of the Internet. |
Tinder | In 2015, the online dating site Tinder was hacked with the aim of stealing all the information of its users. Important information such as real names, dates of birth, postal codes, IP addresses and even sexual preferences... of 4 million accounts were made public on a forum accessed on the Tor browser. In this Internet attack, the attackers actually just wanted to warn about the security holes of the dating platform Tinder, so fortunately there were no cases of abuse or extortion. But Tinder still hasn't woken up, in 2016 they suffered a more serious loss and this time the consequences were 100 times worse. 400 million accounts had their sensitive information stolen, 20 years of data from the giant dating app was officially made public online. The attackers used the Local File Inclusion method (a technique that takes a local file and transfers it directly to the hacker's online resource repository. Many users have spoken out against the leak of extremely sensitive information, even if they had canceled their accounts years ago. The Tinder crisis far exceeds the Internet attack on another online dating platform, Ashley Madison, which exposed 30 million users’ information across 40 countries. |
Maybe you are interested!
-
 Safety Factor of World Banks From 2014 To 2020
Safety Factor of World Banks From 2014 To 2020 -
 Experiences of Some Countries in the World to Ensure Safety of Loans and Lessons for Vietnamese Commercial Banks
Experiences of Some Countries in the World to Ensure Safety of Loans and Lessons for Vietnamese Commercial Banks -
 Identify Rating Levels and Rating Scales
zt2i3t4l5ee
zt2a3gstourism,quan lan,quang ninh,ecology,ecotourism,minh chau,van don,geography,geographical basis,tourism development,science
zt2a3ge
zc2o3n4t5e6n7ts
of the islanders. Therefore, this indicator will be divided into two sub-indicators:
a1. Natural tourism attractiveness a2. Cultural tourism attractiveness
b. Tourist capacity
The two island communes in Quan Lan have different capacities to receive tourists. Minh Chau Commune is home to many standard hotels and resorts, attracting high-income domestic and international tourists. Meanwhile, Quan Lan Commune has many motels mainly built and operated by local people, so the scale and quality are not high, and will be suitable for ordinary tourists such as students.
c. Time of exploitation of Quan Lan Island Commune:
Quan Lan tourism is seasonal due to weather and climate conditions and festivals only take place on certain days of the year, specifically in spring. In Quan Lan commune, the period from April to June and from September to November is considered the best time to visit Quan Lan because the cultural tourism activities are mainly associated with festivals taking place during this time.
Minh Chau island commune:
Tourism exploitation time is all year round, because this is a place with a number of tourist attractions with diverse ecosystems such as Bai Tu Long National Park Research Center, Tram forest, Turtle Laying Beach, so besides coming to the beach for tourism and vacation in the summer, Minh Chau will attract research groups to come for tourism combined with research at other times of the year.
d. Sustainability
The sustainability of ecotourism sites in Quan Lan and Minh Chau communes depends on the sensitivity of the ecosystems to climate changes.
landscape. In general, these tourist destinations have a fairly high level of sustainability, because they are natural ecosystems, planned and protected. However, if a large number of tourists gather at certain times, it can exceed the carrying capacity and affect the sustainability of the environment (polluted beaches, damaged trees, animals moving away from their habitats, etc.), then the sustainability of the above ecosystems (natural ecosystems, human ecosystems) will also be affected and become less sustainable.
e. Location and accessibility
Both island communes have ports to take tourists to visit from Van Don wharf:
- Quan Lan – Van Don traffic route:
Phuc Thinh – Viet Anh high-speed boat and Quang Minh high-speed boat, depart at 8am and 2pm from Van Don to Quan Lan, and at 7am and 1pm from Quan Lan to Van Don. There are also wooden boats departing at 7am and 1pm.
- Van Don - Minh Chau traffic route:
Chung Huong high-speed train, Minh Chau train, morning 7:30 and afternoon 13:30 from Van Don to Minh Chau, morning 6:30 and afternoon 13:00 from Minh Chau to Van Don.
f. Infrastructure
Despite receiving investment attention, the issue of infrastructure and technical facilities for tourism on Quan Lan Island is still an issue that needs to be resolved because it has a direct impact on the implementation of ecotourism activities. The minimum conditions for serving tourists such as accommodation, electricity, water, communication, especially medical services, and security work need to be given top priority. Ecotourism spots in Minh Chau commune are assessed to have better infrastructure and technical facilities for tourism because there are quite complete and synchronous conditions for serving tourists, meeting many needs of domestic and foreign tourists.
3.2.1.4. Determine assessment levels and assessment scales
Corresponding to the levels of each criterion, the index is the score of those levels in the order of 4, 3, 2, 1 decreasing according to the standard of each level: very attractive (4), attractive (3), average (2), less attractive (1).
3.2.1.5. Determining the coefficients of the criteria
For the assessment of DLST in the two communes of Quan Lan and Minh Chau islands, the students added evaluation coefficients to show the importance of the criteria and indicators as follows:
Coefficient 3 with criteria: Attractiveness, Exploitation time. These are the 2 most important criteria for attracting tourists to tourism in general and eco-tourism in particular, so they have the highest coefficient.
Coefficient 2 with criteria: Capacity, Infrastructure, Location and accessibility . Because the assessment area is an island commune of Van Don district, the above criteria are selected by the author with appropriate coefficients at the average level.
Coefficient 1 with criteria: Sustainability. Quan Lan has natural and human-made ecotourism sites, with high biodiversity and little impact from local human factors. Most of the ecotourism sites are still wild, so they are highly sustainable.
3.2.1.6. Results of DLST assessment on Quan Lan island
a. Assessment of the potential for natural tourism development
For Minh Chau commune:
+ Natural tourism attractiveness is determined to be very attractive (4 points) and the most important coefficient (coefficient 3), so the score of the Attractiveness criterion is 4 x 3 = 12.
+ Capacity is determined as average (2 points) and the coefficient is quite important (coefficient 2), then the score of Capacity criterion is 2 x 2 = 4.
+ Exploitation time is long (4 points), the most important coefficient (coefficient 3) so the score of the Exploitation time criterion is 4 x 3 = 12.
+ Sustainability is determined as sustainable (4 points), the important coefficient is the average coefficient (coefficient 1), so the score of the Sustainability criterion is 4 x 1 = 4 points
+ Location and accessibility are determined to be quite favorable (2 points), the coefficient is quite important (coefficient 2), the criterion score is 2 x 2 = 4 points.
+ Infrastructure is assessed as good (3 points), the coefficient is quite important (coefficient 2), then the score of the Infrastructure criterion is 3 x 2 = 6 points.
The total score for evaluating DLST in Minh Chau commune according to 6 evaluation criteria is determined as: 12 + 4 + 12 + 4 + 4 + 6 = 42 points
Similar assessment for Quan Lan commune, we have the following table:
Table 3.3: Assessment of the potential for natural ecotourism development in Quan Lan and Minh Chau communes
Attractiveness of self-tourismof course
Capacity
Mining time
Sustainability
Location and accessibility
Infrastructure
Result
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
CommuneMinh Chau
12
12
4
8
12
12
4
4
4
8
6
8
42/52
Quan CommuneLan
6
12
6
8
9
12
4
4
4
8
4
8
33/52
b. Assessment of the potential for humanistic tourism development
For Quan Lan commune:
+ The attractiveness of human tourism is determined to be very attractive (4 points) and the most important coefficient (coefficient 3), so the score of the Attractiveness criterion is 4 x 3 = 12.
+ Capacity is determined to be large (3 points) and the coefficient is quite important (coefficient 2), then the score of the Capacity criterion is 3 x 2 = 6.
+ Mining time is average (3 points), the most important coefficient (coefficient 3) so the score of the Mining time criterion is 3 x 3 = 9.
+ Sustainability is determined as sustainable (4 points), the important coefficient is the average coefficient (coefficient 1), so the score of the Sustainability criterion is 4 x 1 = 4 points.
+ Location and accessibility are determined to be quite favorable (2 points), the coefficient is quite important (coefficient 2), the criterion score is 2 x 2 = 4 points.
+ Infrastructure is rated as average (2 points), the coefficient is quite important (coefficient 2), then the score of the Infrastructure criterion is 2 x 2 = 4 points.
The total score for evaluating DLST in Quan Lan commune according to 6 evaluation criteria is determined as: 12 + 6 + 6 + 4 + 4 + 4 = 36 points.
Similar assessment with Minh Chau commune we have the following table:
Table 3.4: Assessment of the potential for developing humanistic eco-tourism in Quan Lan and Minh Chau communes
Attractiveness of human tourismliterature
Capacity
Mining time
Sustainability
Location and accessibility
Infrastructure
Result
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Quan CommuneLan
12
12
6
8
9
12
4
4
4
8
4
8
39/52
Minh CommuneChau
6
12
4
8
12
12
4
4
4
8
6
8
36/52
Basically, both Minh Chau and Quan Lan localities have quite favorable conditions for developing ecotourism. However, Quan Lan commune has more advantages to develop ecotourism in a humanistic direction, because this is an area with many famous historical relics such as Quan Lan Communal House, Quan Lan Pagoda, Temple worshiping the hero Tran Khanh Du, ... along with local festivals held annually such as the wind praying ceremony (March 15), Quan Lan festival (June 10-19); due to its location near the port and long exploitation time, the beaches in Quan Lan commune (especially Quan Lan beach) are no longer hygienic and clean to ensure the needs of tourists coming to relax and swim; this is also an area with many beautiful landscapes such as Got Beo wind pass, Ong Phong head, Voi Voi cave, but the ability to access these places is still very limited (dirt hill road, lots of gravel and rocks), especially during rainy and windy times; In addition, other natural resources such as mangrove forests and sea worms have not been really exploited for tourism purposes and ecotourism development. On the contrary, Minh Chau commune has more advantages in developing ecotourism in the direction of natural tourism, this is an area with diverse ecosystems such as at Rua De Beach, Bai Tu Long National Park Conservation Center...; Minh Chau beach is highly appreciated for its natural beauty and cleanliness, ranked in the top ten most beautiful beaches in Vietnam; Minh Chau commune is also home to Tram forest with a large area and a purity of up to 90%, suitable for building bridges through the forest (a very effective type of natural ecotourism currently applied by many countries) for tourists to sightsee, as well as for the purpose of studying and researching.
Figure 3.1: Thenmala Forest Bridge (India) Source: https://www.thenmalaecotourism.com/(August 21, 2019)
3.2.2. Using SWOT matrix to evaluate Quan Lan island tourism
General assessment of current tourism activities of Quan Lan island is shown through the following SWOT matrix:
Table 3.5: SWOT matrix evaluating tourism activities on Quan Lan island
Internal agent
Strengths- There is a lot of potential for tourism development, especially natural ecotourism and humanistic ecotourism.- The unskilled labor force is relatively abundant.- resource environmentunpolluted, still
Weaknesses- Poorly developed infrastructure, especially traffic routes to tourist destinations on the island.- The team of professional staff is still weak.- Tourism products in general
quite wild, originalintact
general and DLST in particularalone is monotonous.
External agents
Opportunity- Tourism is a key industry in the socio-economic development strategy of the province and Van Don economic zone.- Quan Lan was selected as a pilot area for eco-tourism development within the framework of the green growth project between Quang Ninh province and the Japanese organization JICA.- The flow of tourists and especially ecotourism in the world tends toincreasing
Challenge- Weather and climate change abnormally.- Competition in tourism products is increasingly fierce, especially with other localities in the province such as Ha Long, Mong Cai...- Awareness of tourists, especially domestic tourists, about ecotourism and nature conservation is not high.
Through summary analysis using SWOT matrix we see that:
To exploit strengths and take advantage of opportunities, it is necessary to:
- Diversify products and service types (build more tourism routes aimed at specific needs of tourists: experiential tourism immersed in nature, spiritual cultural tourism...)
- Effective exploitation of resources and differentiated products (natural resources and human resources)
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent .s1 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s3 { color: #0D0D0D; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -3pt; } div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -2pt; } div.maincontent .s8 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -1pt; } div.maincontent .s9 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s10 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s11 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s12 { color: black; font-family:Symbol, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s13 { color: black; font-family:Wingdings; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s14 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; } div.maincontent .s15 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; } div.maincontent .s16 { color: black; font-family:Cambria, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s17 { color: #080808; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s18 { color: #080808; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s19 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s20 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10pt; } div.maincontent .s21 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 11pt; } div.maincontent .s22 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s23 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s24 { color: #212121; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; tex
Identify Rating Levels and Rating Scales
zt2i3t4l5ee
zt2a3gstourism,quan lan,quang ninh,ecology,ecotourism,minh chau,van don,geography,geographical basis,tourism development,science
zt2a3ge
zc2o3n4t5e6n7ts
of the islanders. Therefore, this indicator will be divided into two sub-indicators:
a1. Natural tourism attractiveness a2. Cultural tourism attractiveness
b. Tourist capacity
The two island communes in Quan Lan have different capacities to receive tourists. Minh Chau Commune is home to many standard hotels and resorts, attracting high-income domestic and international tourists. Meanwhile, Quan Lan Commune has many motels mainly built and operated by local people, so the scale and quality are not high, and will be suitable for ordinary tourists such as students.
c. Time of exploitation of Quan Lan Island Commune:
Quan Lan tourism is seasonal due to weather and climate conditions and festivals only take place on certain days of the year, specifically in spring. In Quan Lan commune, the period from April to June and from September to November is considered the best time to visit Quan Lan because the cultural tourism activities are mainly associated with festivals taking place during this time.
Minh Chau island commune:
Tourism exploitation time is all year round, because this is a place with a number of tourist attractions with diverse ecosystems such as Bai Tu Long National Park Research Center, Tram forest, Turtle Laying Beach, so besides coming to the beach for tourism and vacation in the summer, Minh Chau will attract research groups to come for tourism combined with research at other times of the year.
d. Sustainability
The sustainability of ecotourism sites in Quan Lan and Minh Chau communes depends on the sensitivity of the ecosystems to climate changes.
landscape. In general, these tourist destinations have a fairly high level of sustainability, because they are natural ecosystems, planned and protected. However, if a large number of tourists gather at certain times, it can exceed the carrying capacity and affect the sustainability of the environment (polluted beaches, damaged trees, animals moving away from their habitats, etc.), then the sustainability of the above ecosystems (natural ecosystems, human ecosystems) will also be affected and become less sustainable.
e. Location and accessibility
Both island communes have ports to take tourists to visit from Van Don wharf:
- Quan Lan – Van Don traffic route:
Phuc Thinh – Viet Anh high-speed boat and Quang Minh high-speed boat, depart at 8am and 2pm from Van Don to Quan Lan, and at 7am and 1pm from Quan Lan to Van Don. There are also wooden boats departing at 7am and 1pm.
- Van Don - Minh Chau traffic route:
Chung Huong high-speed train, Minh Chau train, morning 7:30 and afternoon 13:30 from Van Don to Minh Chau, morning 6:30 and afternoon 13:00 from Minh Chau to Van Don.
f. Infrastructure
Despite receiving investment attention, the issue of infrastructure and technical facilities for tourism on Quan Lan Island is still an issue that needs to be resolved because it has a direct impact on the implementation of ecotourism activities. The minimum conditions for serving tourists such as accommodation, electricity, water, communication, especially medical services, and security work need to be given top priority. Ecotourism spots in Minh Chau commune are assessed to have better infrastructure and technical facilities for tourism because there are quite complete and synchronous conditions for serving tourists, meeting many needs of domestic and foreign tourists.
3.2.1.4. Determine assessment levels and assessment scales
Corresponding to the levels of each criterion, the index is the score of those levels in the order of 4, 3, 2, 1 decreasing according to the standard of each level: very attractive (4), attractive (3), average (2), less attractive (1).
3.2.1.5. Determining the coefficients of the criteria
For the assessment of DLST in the two communes of Quan Lan and Minh Chau islands, the students added evaluation coefficients to show the importance of the criteria and indicators as follows:
Coefficient 3 with criteria: Attractiveness, Exploitation time. These are the 2 most important criteria for attracting tourists to tourism in general and eco-tourism in particular, so they have the highest coefficient.
Coefficient 2 with criteria: Capacity, Infrastructure, Location and accessibility . Because the assessment area is an island commune of Van Don district, the above criteria are selected by the author with appropriate coefficients at the average level.
Coefficient 1 with criteria: Sustainability. Quan Lan has natural and human-made ecotourism sites, with high biodiversity and little impact from local human factors. Most of the ecotourism sites are still wild, so they are highly sustainable.
3.2.1.6. Results of DLST assessment on Quan Lan island
a. Assessment of the potential for natural tourism development
For Minh Chau commune:
+ Natural tourism attractiveness is determined to be very attractive (4 points) and the most important coefficient (coefficient 3), so the score of the Attractiveness criterion is 4 x 3 = 12.
+ Capacity is determined as average (2 points) and the coefficient is quite important (coefficient 2), then the score of Capacity criterion is 2 x 2 = 4.
+ Exploitation time is long (4 points), the most important coefficient (coefficient 3) so the score of the Exploitation time criterion is 4 x 3 = 12.
+ Sustainability is determined as sustainable (4 points), the important coefficient is the average coefficient (coefficient 1), so the score of the Sustainability criterion is 4 x 1 = 4 points
+ Location and accessibility are determined to be quite favorable (2 points), the coefficient is quite important (coefficient 2), the criterion score is 2 x 2 = 4 points.
+ Infrastructure is assessed as good (3 points), the coefficient is quite important (coefficient 2), then the score of the Infrastructure criterion is 3 x 2 = 6 points.
The total score for evaluating DLST in Minh Chau commune according to 6 evaluation criteria is determined as: 12 + 4 + 12 + 4 + 4 + 6 = 42 points
Similar assessment for Quan Lan commune, we have the following table:
Table 3.3: Assessment of the potential for natural ecotourism development in Quan Lan and Minh Chau communes
Attractiveness of self-tourismof course
Capacity
Mining time
Sustainability
Location and accessibility
Infrastructure
Result
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
CommuneMinh Chau
12
12
4
8
12
12
4
4
4
8
6
8
42/52
Quan CommuneLan
6
12
6
8
9
12
4
4
4
8
4
8
33/52
b. Assessment of the potential for humanistic tourism development
For Quan Lan commune:
+ The attractiveness of human tourism is determined to be very attractive (4 points) and the most important coefficient (coefficient 3), so the score of the Attractiveness criterion is 4 x 3 = 12.
+ Capacity is determined to be large (3 points) and the coefficient is quite important (coefficient 2), then the score of the Capacity criterion is 3 x 2 = 6.
+ Mining time is average (3 points), the most important coefficient (coefficient 3) so the score of the Mining time criterion is 3 x 3 = 9.
+ Sustainability is determined as sustainable (4 points), the important coefficient is the average coefficient (coefficient 1), so the score of the Sustainability criterion is 4 x 1 = 4 points.
+ Location and accessibility are determined to be quite favorable (2 points), the coefficient is quite important (coefficient 2), the criterion score is 2 x 2 = 4 points.
+ Infrastructure is rated as average (2 points), the coefficient is quite important (coefficient 2), then the score of the Infrastructure criterion is 2 x 2 = 4 points.
The total score for evaluating DLST in Quan Lan commune according to 6 evaluation criteria is determined as: 12 + 6 + 6 + 4 + 4 + 4 = 36 points.
Similar assessment with Minh Chau commune we have the following table:
Table 3.4: Assessment of the potential for developing humanistic eco-tourism in Quan Lan and Minh Chau communes
Attractiveness of human tourismliterature
Capacity
Mining time
Sustainability
Location and accessibility
Infrastructure
Result
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Point
DarkMulti
Quan CommuneLan
12
12
6
8
9
12
4
4
4
8
4
8
39/52
Minh CommuneChau
6
12
4
8
12
12
4
4
4
8
6
8
36/52
Basically, both Minh Chau and Quan Lan localities have quite favorable conditions for developing ecotourism. However, Quan Lan commune has more advantages to develop ecotourism in a humanistic direction, because this is an area with many famous historical relics such as Quan Lan Communal House, Quan Lan Pagoda, Temple worshiping the hero Tran Khanh Du, ... along with local festivals held annually such as the wind praying ceremony (March 15), Quan Lan festival (June 10-19); due to its location near the port and long exploitation time, the beaches in Quan Lan commune (especially Quan Lan beach) are no longer hygienic and clean to ensure the needs of tourists coming to relax and swim; this is also an area with many beautiful landscapes such as Got Beo wind pass, Ong Phong head, Voi Voi cave, but the ability to access these places is still very limited (dirt hill road, lots of gravel and rocks), especially during rainy and windy times; In addition, other natural resources such as mangrove forests and sea worms have not been really exploited for tourism purposes and ecotourism development. On the contrary, Minh Chau commune has more advantages in developing ecotourism in the direction of natural tourism, this is an area with diverse ecosystems such as at Rua De Beach, Bai Tu Long National Park Conservation Center...; Minh Chau beach is highly appreciated for its natural beauty and cleanliness, ranked in the top ten most beautiful beaches in Vietnam; Minh Chau commune is also home to Tram forest with a large area and a purity of up to 90%, suitable for building bridges through the forest (a very effective type of natural ecotourism currently applied by many countries) for tourists to sightsee, as well as for the purpose of studying and researching.
Figure 3.1: Thenmala Forest Bridge (India) Source: https://www.thenmalaecotourism.com/(August 21, 2019)
3.2.2. Using SWOT matrix to evaluate Quan Lan island tourism
General assessment of current tourism activities of Quan Lan island is shown through the following SWOT matrix:
Table 3.5: SWOT matrix evaluating tourism activities on Quan Lan island
Internal agent
Strengths- There is a lot of potential for tourism development, especially natural ecotourism and humanistic ecotourism.- The unskilled labor force is relatively abundant.- resource environmentunpolluted, still
Weaknesses- Poorly developed infrastructure, especially traffic routes to tourist destinations on the island.- The team of professional staff is still weak.- Tourism products in general
quite wild, originalintact
general and DLST in particularalone is monotonous.
External agents
Opportunity- Tourism is a key industry in the socio-economic development strategy of the province and Van Don economic zone.- Quan Lan was selected as a pilot area for eco-tourism development within the framework of the green growth project between Quang Ninh province and the Japanese organization JICA.- The flow of tourists and especially ecotourism in the world tends toincreasing
Challenge- Weather and climate change abnormally.- Competition in tourism products is increasingly fierce, especially with other localities in the province such as Ha Long, Mong Cai...- Awareness of tourists, especially domestic tourists, about ecotourism and nature conservation is not high.
Through summary analysis using SWOT matrix we see that:
To exploit strengths and take advantage of opportunities, it is necessary to:
- Diversify products and service types (build more tourism routes aimed at specific needs of tourists: experiential tourism immersed in nature, spiritual cultural tourism...)
- Effective exploitation of resources and differentiated products (natural resources and human resources)
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent .s1 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s3 { color: #0D0D0D; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -3pt; } div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -2pt; } div.maincontent .s8 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -1pt; } div.maincontent .s9 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s10 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s11 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s12 { color: black; font-family:Symbol, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s13 { color: black; font-family:Wingdings; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s14 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; } div.maincontent .s15 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; } div.maincontent .s16 { color: black; font-family:Cambria, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s17 { color: #080808; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s18 { color: #080808; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s19 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s20 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10pt; } div.maincontent .s21 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 11pt; } div.maincontent .s22 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s23 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s24 { color: #212121; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; tex -
 Analyzing Customer Reviews About The Official Website Of Hues Discount Card Program Of Tan Nguyen Mtv Company Limited.
Analyzing Customer Reviews About The Official Website Of Hues Discount Card Program Of Tan Nguyen Mtv Company Limited. -
 Complete the retail process of kitchen utensils at Website Hanoi.Golmart.vn - 9
Complete the retail process of kitchen utensils at Website Hanoi.Golmart.vn - 9
Time and damage | |
Equifax | Equifax - A credit company in the US, in a report revealed that they had to deal with a crisis due to an Internet attack for many months in a row. They discovered the attack in July 2017. The leaked information published included a lot of confidential personal data of 143 million customers in the US, Canada, UK and nearly 200,000 credit card information. There was almost no way for the company to recover the leaked information after the 2017 Internet attack, this error was determined to be due to a vulnerability in Apache Struts that was thoroughly exploited by hackers. The consequences were so great that major shareholders and executives of this company had to sell their shares to escape this crisis. |
Target | The second largest retail chain in the US was the victim of a large-scale Internet attack in December 2013. Data of 110 million customers was stolen from November 27 to December 15. Of these, up to 40 million customers had all their information stolen (name, address, phone number and email, bank account...) and 70 million other customers had their information almost completely stolen. What is more worrying is that the unit that discovered Target was attacked was not Target. A security company in the US accidentally discovered this and at the same time they also discovered that this group was operating in Eastern Europe. The hackers secretly installed malware on the victims' computers and then recorded and sent credit card information. At the same time, they later offered a ransom of $18 million for all the data on black market websites. |
Website name
7.4.4. Security measures for Website
7.4.4.1. Server Security
To have a well-functioning website, first of all, it is necessary to prepare well the computer system that acts as the server (where the applications that allow us to put our websites on the Internet will be installed and also where the database of the website we want to put on the Internet is stored). To do so, it is necessary to carefully study the requirements for our website, from which to make effective technical choices. The information to consider when choosing a Web server is:
(1) Server configuration, including: hard drive capacity, main memory capacity, processing speed, number of chips,... When choosing this hardware device, it is necessary to base on an important criterion which is the number of connections that the server can handle in a unit of time.
(2) The operating system that will be used for your Web server. Currently, there are many operating systems used for server systems such as Windows NT, Windows 2000 Server, Unix,...
(3) Web Server software such as Microsoft's IIS or Apache.
(4) Server system management and security software,... Also need to pay attention to the following parameters:
(1) Response time to user requests, usually measured by the number of connections the server can handle in a unit of time.
(2) Throughput: measured by the number of bytes of data that can be received in a unit of time.
It is necessary to have initial investigations and estimates of the number of people who will access your website in a unit of time, through which the most effective choice can be made. For units that are not specialized in information technology, the best way is to use specialized intermediary consultants for this choice.
7.4.4.2. Security policies for Website servers
After building a website, this is where we can post promotional information about the company's image as well as introduce the products we sell, so we need to regularly maintain the stable operation of this website. To do so, in addition to choosing a strong enough hardware system and suitable Web Server software, we need to have policies to protect the information stored.
kept on the Web server as well as against attacks on this server system:
(1) There are mechanisms to record server activity logs, usually this feature is integrated into server operating systems.
(2) The Web server should not be connected directly to the Internet, but should be connected through a Router with a Firewall installed. In addition, Firewall or Proxy software can be installed to control information coming in and out of the server.
(3) Back up all data in the Web server to another storage device to prevent data damage. If economic conditions allow, there should be other servers used as data backup machines, which are essentially copies of our Web server.
(4) Disable unused Web services that are built into the operating system or Web management software.
(5) There is a mechanism for decentralization for users.
(6) There are mechanisms in place to protect physical devices from damage or theft.
(7) Be careful when installing new software or running programs on the server, avoid using software or programs of unknown origin because they can be a source of spreading viruses to our computers.
(8) There should be backup Host addresses (Host is the address of the Web server on the network) in case the main address is attacked or overloaded, then everyone will be allowed to use this backup address.
7.4.4.3. Increase security for commercial websites
This is the key solution to ensure the safety of commercial websites. The security infrastructure of commercial websites is mainly related to protecting commercial servers. The directions for improving and developing the security infrastructure of commercial websites are:
(1) Access control and authentication : This involves the completion of public key infrastructure, the construction of digital certificate infrastructure and electronic signatures on a regional and international scale to ensure that any transactions between clients and the commercial website server are controlled and authenticated. For user authentication by name and password, the user (Admin) must control the confidentiality of the password to prevent illegal use.
(2) Operating system controls : The operating system provides a secure infrastructure for the commercial website server. Businesses with commercial websites are recommended to use the UNIX operating system for the Web server, which has high protection against unauthorized access and ensures server data integrity.
(3) Protect the server-client system and transmission channels: Use authentication mechanisms and measures to protect the Website server and clients during transmission.
7.4.4.4. Protection of commercial clients and servers
Clients must be protected against threats that originate from software or data downloaded to the client from the Internet. Web pages are often delivered to the client upon request by the Web browser. Dynamic content is also delivered over the Internet through dynamic Web pages. These can pose threats to clients.
Other threats to the client can be browser hijackers, email attachments, cookies, and web spoofing.
Commerce servers are at the heart of e-commerce security. Commerce servers (commerce Web servers) respond to requests from browsers.
Web browsing via HTTP protocol and CGI Scripts need to be strictly protected by strong measures.
7.5. SOCIAL MEDIA SECURITY
7.5.1. Introduction to social media
Media is a specific method that helps businesses convey messages and content of their marketing strategy to customers. The goal is to reach potential customers, helping to increase conversion rates for businesses.
Media channels have a great influence on a business's marketing campaign. If chosen appropriately, media channels can help businesses receive good feedback from customers, boost sales and increase their competitiveness.
The media is increasingly perfected and has the ability to convey information accurately and effectively to users. Popular media today include newspapers, television, the Internet, radio, books, advertisements, tapes, and direct telephone calls.
Social media is the media that uses technology platforms based on the Internet. Basically, social media is divided into 4 basic groups as follows:
First is Social Community: This group will focus on developing networks of relationships and connecting people with similar interests and hobbies. The most prominent are social networks such as Facebook and Twitter. The highlight of Social Community is its multi-dimensional interaction. It allows users to connect, chat and share information.
Second is Social Publishing: These are websites that transmit and disseminate content online. These include blogs; news sites; microsites; pages that post documents, music, videos, images, etc.