


( (
Maybe you are interested!
-
 Solution to improve the efficiency of receiving and delivering full container export goods by sea at Viet Hoa Transport and Trading Service Co., Ltd. - 1
Solution to improve the efficiency of receiving and delivering full container export goods by sea at Viet Hoa Transport and Trading Service Co., Ltd. - 1 -
 The main solution to improve the production and business efficiency of Agricultural and Food Industry Printing Company - 2
The main solution to improve the production and business efficiency of Agricultural and Food Industry Printing Company - 2 -
 Solutions for tourism development in Tien Lang - 10
zt2i3t4l5ee
zt2a3gstourism, tourism development
zt2a3ge
zc2o3n4t5e6n7ts
- District People's Committees and authorities of communes with tourist attractions should support, promote, and provide necessary information to people, helping them improve their knowledge about tourism. Raise tourism awareness for local people.
*
* *
Due to limited knowledge and research time, the thesis inevitably has shortcomings. Therefore, I look forward to receiving guidance from teachers, experts as well as your comments to make the thesis more complete.
Chapter III Conclusion
Through the issues presented in Chapter II, we can come to some conclusions:
Based on the strengths of available tourism resources, the types of tourism in Tien Lang that need to be promoted in the coming time are sightseeing and resort tourism, discovery tourism, weekend tourism. To improve the quality and diversify tourism products, Tien Lang district needs to combine with local cultural tourism resources, at the same time combine with surrounding areas, build rich tourism products. The strengths of Tien Lang tourism are eco-tourism and cultural tourism, so developing Tien Lang tourism must always go hand in hand with restoring and preserving types of cultural tourism resources. Some necessary measures to support and improve the efficiency of exploiting tourism resources in Tien Lang are: strengthening the construction of technical facilities and labor force serving tourism, actively promoting and advertising tourism, and expanding forms of capital mobilization for tourism development.
CONCLUDE
I Conclusion
1. Based on the results achieved within the framework of the thesis's needs, some basic conclusions can be drawn as follows:
Tien Lang is a locality with great potential for tourism development. The relatively abundant cultural tourism resources and ecological tourism resources have great appeal to tourists. Based on this potential, Tien Lang can build a unique tourism industry that is competitive enough with other localities within Hai Phong city and neighboring areas.
In recent years, the exploitation of the advantages of resources to develop tourism and build tourist routes in Tien Lang has not been commensurate with the available potential. In terms of quantity, many resource objects have not been brought into the purpose of tourism development. In terms of time, the regular service time has not been extended to attract more visitors. Infrastructure and technical facilities are still weak. The labor force is still thin and weak in terms of expertise. Tourism programs and routes have not been organized properly, the exploitation content is still monotonous, so it has not attracted many visitors. Although resources have not been mobilized much for tourism development, they are facing the risk of destruction and degradation.
2. Based on the results of investigation, analysis, synthesis, evaluation and selective absorption of research results of related topics, the thesis has proposed a number of necessary solutions to improve the efficiency of exploiting tourism resources in Tien Lang such as: promoting the restoration and conservation of tourism resources, focusing on investment and key exploitation of ecotourism resources, strengthening the construction of infrastructure and tourism workforce. Expanding forms of capital mobilization. In addition, the thesis has built a number of tourist routes of Hai Phong in which Tien Lang tourism resources play an important role.
Exploiting Tien Lang tourism resources for tourism development is currently facing many difficulties. The above measures, if applied synchronously, will likely bring new prospects for the local tourism industry, contributing to making Tien Lang tourism an important economic sector in the district's economic structure.
REFERENCES
1. Nhuan Ha, Trinh Minh Hien, Tran Phuong, Hai Phong - Historical and cultural relics, Hai Phong Publishing House, 1993
2. Hai Phong City History Council, Hai Phong Gazetteer, Hai Phong Publishing House, 1990.
3. Hai Phong City History Council, History of Tien Lang District Party Committee, Hai Phong Publishing House, 1990.
4. Hai Phong City History Council, University of Social Sciences and Humanities, VNU, Hai Phong Place Names Encyclopedia, Hai Phong Publishing House. 2001.
5. Law on Cultural Heritage and documents guiding its implementation, National Political Publishing House, Hanoi, 2003.
6. Tran Duc Thanh, Lecture on Tourism Geography, Faculty of Tourism, University of Social Sciences and Humanities, VNU, 2006
7. Hai Phong Center for Social Sciences and Humanities, Some typical cultural heritages of Hai Phong, Hai Phong Publishing House, 2001
8. Nguyen Ngoc Thao (editor-in-chief, Tourism Geography, Hai Phong Publishing House, two volumes (2001-2002)
9. Nguyen Minh Tue and group of authors, Hai Phong Tourism Geography, Ho Chi Minh City Publishing House, 1997.
10. Nguyen Thanh Son, Hai Phong Tourism Territory Organization, Associate Doctoral Thesis in Geological Geography, Hanoi, 1996.
11. Decision No. 2033/QD – UB on detailed planning of Tien Lang town, Hai Phong city until 2020.
12. Department of Culture, Information, Hai Phong Museum, Hai Phong relics
- National ranked scenic spot, Hai Phong Publishing House, 2005. 13. Tien Lang District People's Committee, Economic Development Planning -
Culture - Society of Tien Lang district to 2010.
14.Website www.HaiPhong.gov.vn
APPENDIX 1
List of national ranked monuments
STT
Name of the monument
Number, year of decisiondetermine
Location
1
Gam Temple
938 VH/QĐ04/08/1992
Cam Khe Village- Toan Thang commune
2
Doc Hau Temple
9381 VH/QĐ04/08/1992
Doc Hau Village –Toan Thang commune
3
Cuu Doi Communal House
3207 VH/QĐDecember 30, 1991
Zone II of townTien Lang
4
Ha Dai Temple
938 VH/QĐ04/08/1992
Ha Dai Village –Tien Thanh commune
APPENDIX II
STT
Name of the monument
Number, year of decision
Location
1
Phu Ke Pagoda Temple
178/QD-UBJanuary 28, 2005
Zone 1 - townTien Lang
2
Trung Lang Temple
178/QD-UBJanuary 28, 2005
Zone 4 – townTien Lang
3
Bao Khanh Pagoda
1900/QD-UBAugust 24, 2006
Nam Tu Village -Kien Thiet commune
4
Bach Da Pagoda
1792/QD-UB11/11/2002
Hung Thang Commune
5
Ngoc Dong Temple
177/QD-UBNovember 27, 2005
Tien Thanh Commune
6
Tomb of Minister TSNhu Van Lan
2848/QD-UBSeptember 19, 2003
Nam Tu Village -Kien Thiet commune
7
Canh Son Stone Temple
2160/QD-UBSeptember 19, 2003
Van Doi Commune –Doan Lap
8
Meiji Temple
2259/QD-UBSeptember 19, 2002
Toan Thang Commune
9
Tien Doi Noi Temple
477/QD-UBSeptember 19, 2005
Doan Lap Commune
10
Tu Doi Temple
177/QD-UBJanuary 28, 2005
Doan Lap Commune
11
Duyen Lao Temple
177/QD-UBJanuary 28, 2005
Tien Minh Commune
12
Dinh Xuan Uc Pagoda
177/QD-UBJanuary 28, 2005
Bac Hung Commune
13
Chu Khe Pagoda
177/QD-UBJanuary 28, 2005
Hung Thang Commune
14
Dong Dinh
2848/QD-UBNovember 21, 2002
Vinh Quang Commune
15
President's Memorial HouseTon Duc Thang
177/QD-UBJanuary 28, 2005
NT Quy Cao
Ha Dai Temple
Ben Vua Temple
Tien Lang hot spring
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent .s1 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; font-size: 16pt; } div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s3 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; font-size: 14pt; } div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; font-size: 14pt; } div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s8 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 6pt; } div.maincontent .s9 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 12pt; } div.maincontent .s11 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; tex
Solutions for tourism development in Tien Lang - 10
zt2i3t4l5ee
zt2a3gstourism, tourism development
zt2a3ge
zc2o3n4t5e6n7ts
- District People's Committees and authorities of communes with tourist attractions should support, promote, and provide necessary information to people, helping them improve their knowledge about tourism. Raise tourism awareness for local people.
*
* *
Due to limited knowledge and research time, the thesis inevitably has shortcomings. Therefore, I look forward to receiving guidance from teachers, experts as well as your comments to make the thesis more complete.
Chapter III Conclusion
Through the issues presented in Chapter II, we can come to some conclusions:
Based on the strengths of available tourism resources, the types of tourism in Tien Lang that need to be promoted in the coming time are sightseeing and resort tourism, discovery tourism, weekend tourism. To improve the quality and diversify tourism products, Tien Lang district needs to combine with local cultural tourism resources, at the same time combine with surrounding areas, build rich tourism products. The strengths of Tien Lang tourism are eco-tourism and cultural tourism, so developing Tien Lang tourism must always go hand in hand with restoring and preserving types of cultural tourism resources. Some necessary measures to support and improve the efficiency of exploiting tourism resources in Tien Lang are: strengthening the construction of technical facilities and labor force serving tourism, actively promoting and advertising tourism, and expanding forms of capital mobilization for tourism development.
CONCLUDE
I Conclusion
1. Based on the results achieved within the framework of the thesis's needs, some basic conclusions can be drawn as follows:
Tien Lang is a locality with great potential for tourism development. The relatively abundant cultural tourism resources and ecological tourism resources have great appeal to tourists. Based on this potential, Tien Lang can build a unique tourism industry that is competitive enough with other localities within Hai Phong city and neighboring areas.
In recent years, the exploitation of the advantages of resources to develop tourism and build tourist routes in Tien Lang has not been commensurate with the available potential. In terms of quantity, many resource objects have not been brought into the purpose of tourism development. In terms of time, the regular service time has not been extended to attract more visitors. Infrastructure and technical facilities are still weak. The labor force is still thin and weak in terms of expertise. Tourism programs and routes have not been organized properly, the exploitation content is still monotonous, so it has not attracted many visitors. Although resources have not been mobilized much for tourism development, they are facing the risk of destruction and degradation.
2. Based on the results of investigation, analysis, synthesis, evaluation and selective absorption of research results of related topics, the thesis has proposed a number of necessary solutions to improve the efficiency of exploiting tourism resources in Tien Lang such as: promoting the restoration and conservation of tourism resources, focusing on investment and key exploitation of ecotourism resources, strengthening the construction of infrastructure and tourism workforce. Expanding forms of capital mobilization. In addition, the thesis has built a number of tourist routes of Hai Phong in which Tien Lang tourism resources play an important role.
Exploiting Tien Lang tourism resources for tourism development is currently facing many difficulties. The above measures, if applied synchronously, will likely bring new prospects for the local tourism industry, contributing to making Tien Lang tourism an important economic sector in the district's economic structure.
REFERENCES
1. Nhuan Ha, Trinh Minh Hien, Tran Phuong, Hai Phong - Historical and cultural relics, Hai Phong Publishing House, 1993
2. Hai Phong City History Council, Hai Phong Gazetteer, Hai Phong Publishing House, 1990.
3. Hai Phong City History Council, History of Tien Lang District Party Committee, Hai Phong Publishing House, 1990.
4. Hai Phong City History Council, University of Social Sciences and Humanities, VNU, Hai Phong Place Names Encyclopedia, Hai Phong Publishing House. 2001.
5. Law on Cultural Heritage and documents guiding its implementation, National Political Publishing House, Hanoi, 2003.
6. Tran Duc Thanh, Lecture on Tourism Geography, Faculty of Tourism, University of Social Sciences and Humanities, VNU, 2006
7. Hai Phong Center for Social Sciences and Humanities, Some typical cultural heritages of Hai Phong, Hai Phong Publishing House, 2001
8. Nguyen Ngoc Thao (editor-in-chief, Tourism Geography, Hai Phong Publishing House, two volumes (2001-2002)
9. Nguyen Minh Tue and group of authors, Hai Phong Tourism Geography, Ho Chi Minh City Publishing House, 1997.
10. Nguyen Thanh Son, Hai Phong Tourism Territory Organization, Associate Doctoral Thesis in Geological Geography, Hanoi, 1996.
11. Decision No. 2033/QD – UB on detailed planning of Tien Lang town, Hai Phong city until 2020.
12. Department of Culture, Information, Hai Phong Museum, Hai Phong relics
- National ranked scenic spot, Hai Phong Publishing House, 2005. 13. Tien Lang District People's Committee, Economic Development Planning -
Culture - Society of Tien Lang district to 2010.
14.Website www.HaiPhong.gov.vn
APPENDIX 1
List of national ranked monuments
STT
Name of the monument
Number, year of decisiondetermine
Location
1
Gam Temple
938 VH/QĐ04/08/1992
Cam Khe Village- Toan Thang commune
2
Doc Hau Temple
9381 VH/QĐ04/08/1992
Doc Hau Village –Toan Thang commune
3
Cuu Doi Communal House
3207 VH/QĐDecember 30, 1991
Zone II of townTien Lang
4
Ha Dai Temple
938 VH/QĐ04/08/1992
Ha Dai Village –Tien Thanh commune
APPENDIX II
STT
Name of the monument
Number, year of decision
Location
1
Phu Ke Pagoda Temple
178/QD-UBJanuary 28, 2005
Zone 1 - townTien Lang
2
Trung Lang Temple
178/QD-UBJanuary 28, 2005
Zone 4 – townTien Lang
3
Bao Khanh Pagoda
1900/QD-UBAugust 24, 2006
Nam Tu Village -Kien Thiet commune
4
Bach Da Pagoda
1792/QD-UB11/11/2002
Hung Thang Commune
5
Ngoc Dong Temple
177/QD-UBNovember 27, 2005
Tien Thanh Commune
6
Tomb of Minister TSNhu Van Lan
2848/QD-UBSeptember 19, 2003
Nam Tu Village -Kien Thiet commune
7
Canh Son Stone Temple
2160/QD-UBSeptember 19, 2003
Van Doi Commune –Doan Lap
8
Meiji Temple
2259/QD-UBSeptember 19, 2002
Toan Thang Commune
9
Tien Doi Noi Temple
477/QD-UBSeptember 19, 2005
Doan Lap Commune
10
Tu Doi Temple
177/QD-UBJanuary 28, 2005
Doan Lap Commune
11
Duyen Lao Temple
177/QD-UBJanuary 28, 2005
Tien Minh Commune
12
Dinh Xuan Uc Pagoda
177/QD-UBJanuary 28, 2005
Bac Hung Commune
13
Chu Khe Pagoda
177/QD-UBJanuary 28, 2005
Hung Thang Commune
14
Dong Dinh
2848/QD-UBNovember 21, 2002
Vinh Quang Commune
15
President's Memorial HouseTon Duc Thang
177/QD-UBJanuary 28, 2005
NT Quy Cao
Ha Dai Temple
Ben Vua Temple
Tien Lang hot spring
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent .s1 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; font-size: 16pt; } div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s3 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; font-size: 14pt; } div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; font-size: 14pt; } div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; } div.maincontent .s8 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 6pt; } div.maincontent .s9 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 12pt; } div.maincontent .s11 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; tex -
 Solutions to Improve Business Efficiency of Vietnam Technological and Commercial Joint Stock Bank
Solutions to Improve Business Efficiency of Vietnam Technological and Commercial Joint Stock Bank -
 Principles and Tools for Problem Solving to Improve Business Efficiency
Principles and Tools for Problem Solving to Improve Business Efficiency


gWorker = i;
EndIf Else


//Prioritize by calculation ability If






Endif EndFor
EndIf EndIf
Endif
gWorker = i;
If (bWorker exists)
return bWorker;
EndIf
If (gWorker exists)
return gWorker;
EndIf
Return NULL;
Next, I will validate the availability of reliability-based scheduling schemes using simulation results in section 5.
Chapter 4. EXPERIMENTAL RESULTS
This section introduces the simulation program, simulation scenarios, and discusses the simulation results.
4.1 Simulation program
In this section, I will present the simulation program used in my thesis, the VCSIM simulation program. VCSIM is built on the event-driven model. This is the model used in BOINC. VCSIM simulates the creation and distribution of tasks executed in a highly variable, heterogeneous and distributed environment. In addition, it collects and evaluates the efficiency of completed tasks. VCSIM is written in the C programming language.
VCSIM is designed with main modules: Workstation management module, job management module, simulation module. The workstation management module performs the task of creating a list of workstations with the same initial reliability, with different calculation times, creating fake machines, managing workstations such as taking workstations from the queue according to scheduling criteria, pushing workstations into the queue... The job management module performs the task of creating a list of tasks, assigning tasks to workstations, managing the job queue, calculating the reliability of tasks... The simulation module performs the task of managing a list of simulation parameters such as the number of simulations, the number of workstations performed, the number of jobs performed, the error fraction, the acceptable error rate, the number of re-execution times of tasks, the sabotage rate, the execution scheduling scheme, the point check rate, whether the parameter supports blacklisting or not, whether the parameter supports point checking by voting or not... Perform simulations, support display functions and output results.
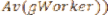
4.2 Simulation scenario
In this section, I determine the efficiency of the proposed scheduling scheme by simulations. In my simulation, a computation consists of a list of N
independent tasks of equal size and a list P of volunteer computers (workstations). To simulate the sabotage of rogue machines, a fraction f =
0.2 of the randomly selected workstations are destructive. There are two cases regarding the number of tasks and workstations of interest.
In the first case ( N > P ), there are 1500 tasks and 500 workstations, in the second case ( N < P ), there are 500 and 1500 workstations. Assuming that the blacklist policy is not applied (i.e. a workstation can submit results even after it is detected as a saboteur), a voting-based checkpointing technique is used in the simulation. Because the performance of a reliability-based scheduling scheme is evaluated in terms of the delay parameter (i.e. the ratio of the running time of the computation with or without fault tolerance), I can assume that the execution time of a task on a workstation is a random number between 1 and 5 time units. The main purpose of this simulation is to compare the performance of the following scheduling schemes: Round Robin RR, Round Robin scheduling based on the priority of the implementation of PRR(Av), Round Robin scheduling based on the priority of reliability PRR(Cr), Round Robin scheduling based on the reliability test with the priority of reliability CRR(Cr) and the priority of the implementation of CRR(Av). To ensure the reliability of the simulation results, I will simulate each case 5 times and take the average value.
4.3 Results
Figures 4-1, 4-2, 4-3, 4-4, show the experimental results for different error rate cases when the number of jobs is larger than the number of machines and Figures 4-5, 4-6, 4-7, 4-8 show the experimental results for different error rate cases when the number of jobs is smaller than the number of workstations, obtained from simulation for concurrent scheduling schemes, I plot the value of the slowdown parameter against other parameters because it is an important performance parameter when adopting a reliability-based fault-tolerant scheme in volunteer computing systems.
Looking at the results of the comparison chart I see that the scheduling schemes I proposed significantly reduce the execution time compared to the Round Robin scheduling scheme.






respectively. In particular, in both cases N > P or N < P , the CRR scheduling scheme is reduced by 40% - 60% compared to the corresponding RR scheduling scheme. In both cases N > P or N < P ,



The CRR scheduling scheme reduces approximately 60% - 80% compared to the corresponding RR scheduling scheme. In the case of N > P, N < P , the CRR scheduling scheme is more efficient than PRR(Cr) and PRR(Av) except for the case of N < P and the error rate of the result
less than 0.001. The PRR(Cr) scheduling scheme is slightly more efficient than PRR(Av) when the error rate is less than 0.001. The rest are almost equivalent.
The reason why the schemes have such good results is because the schemes have paid attention to choosing workstations to improve the reliability of the task after each workstation calculation so that the reliability of the task quickly moves towards the reliability threshold.
Figure 4-1. Comparison chart of delays of scheduling schemes with s= 0.25,N >P
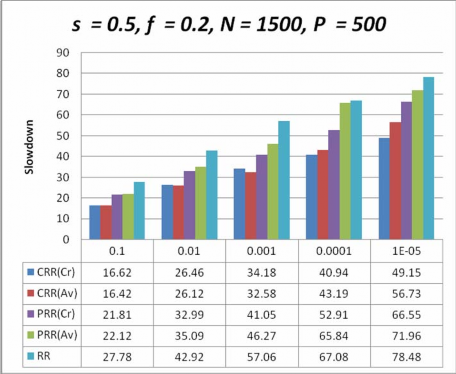
Figure 4-2. Comparison chart of delays of scheduling schemes with s= 0.5,N >P
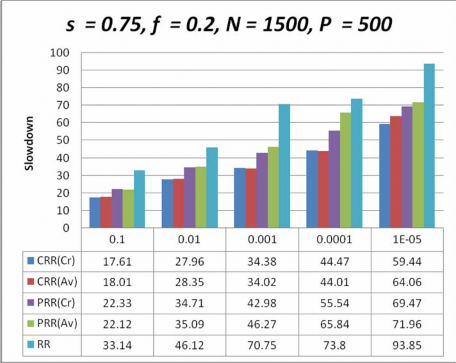
Figure 4-3 Comparison chart of delays of scheduling schemes with s= 0.75,N >P
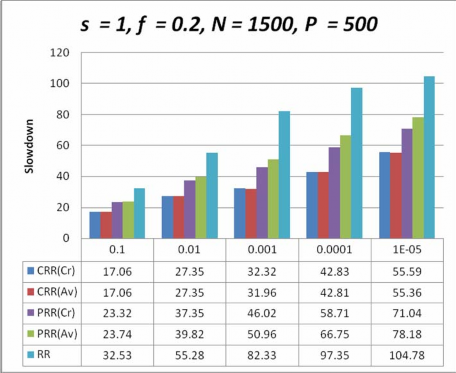
Figure 4-4. Comparison chart of delays of scheduling schemes with s= 1,N >P
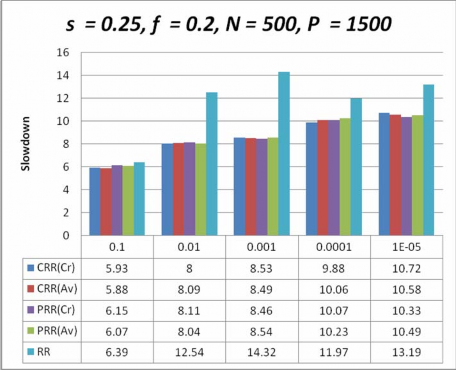
Figure 4-5. Comparison chart of delays of scheduling schemes with s= 0.25,N< P
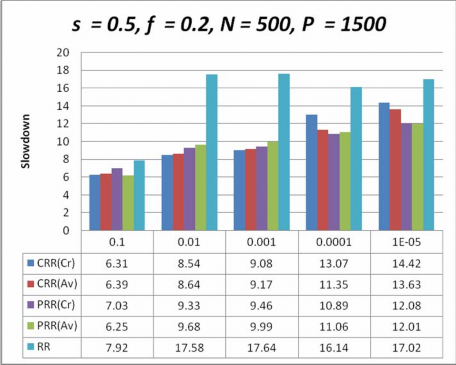
Figure 4-6. Comparison chart of delays of scheduling schemes with s= 0.5,N< P
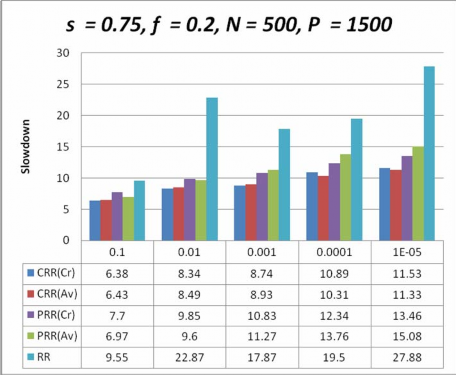
Figure 4-7. Comparison chart of delays of scheduling schemes with s= 0.75,N< P
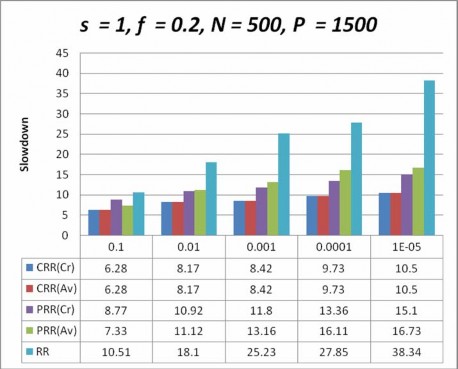
Figure 4-8. Comparison chart of delays of scheduling schemes with s= 1,N< P





