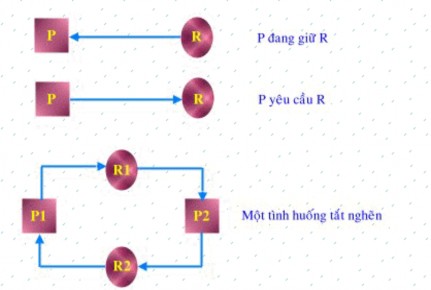
Figure 3.19 Resource allocation graph
Methods of handling blockages
There are mainly three approaches to dealing with blockages:
Use a protocol to ensure that the system never gets stuck.
Allow blockages to occur and seek to correct them.
Completely ignore congestion handling, pretending the system never gets congested.
Prevent blockages
For congestion to not occur, at least one of the four conditions must not occur:
Non-shareable resources: In general, it is almost impossible to avoid this condition because the nature of the resource is almost fixed. However, for some rendering resources, one can use spooling mechanisms to transform them into sharable resources.
Resource reservation and request: it must be ensured that whenever a process requests a resource, it does not reserve other resources. One of the following two access mechanisms can be implemented:
The process must request all necessary resources before starting processing.
=> The difficulty with this method is that it is difficult for the process to accurately estimate the resources needed because the demand may depend on the processing. In addition, if the process occupies resources that are not needed immediately, the use of resources will be inefficient.
When a process requests a new resource and is denied, it must release the resources it is holding, and then reallocate them again at the same time as the new resource.
=> This method raises difficulties in protecting the data integrity of the system.
No resource reclaim: allows the system to reclaim resources from locked processes and re-allocate them to the process when it is released from the locked state. However, with some types of resources, reclaiming will be very difficult because it violates data integrity.
Existence of a cycle: avoid creating cycles in the graph by allocating resources according to a hierarchy like this:
Let R = {R 1 , R 2 ,...,Rm} be the set of resource types. Resource types are ranked from 1-N.
For example : F(disk) = 2, F(printer) = 12
Processes when requesting resources must comply with the rule: when a process is holding resource Ri, it can only request resources Rj if F(Rj) > F(Ri).
Avoid congestion
Congestion prevention is a major concern when it comes to resource utilization. Congestion avoidance is the elimination of all opportunities that could lead to congestion in the future. Complex mechanisms are required to accomplish this.
Some basic concepts
Safe state : State A is safe if the system can satisfy the resource demands (up to the maximum) of each process in a certain order while still preventing deadlock.
A safe allocation sequence: an order of processes <P 1 , P 2 ,...,Pn> is safe for the current allocation state if for each process Pi the resource demand of Pi can be satisfied with the free resources of the system, plus the resources currently held by other processes Pj, with j<i.
A safe state cannot be a deadlocked state. Conversely, an unsafe state can lead to a deadlocked state.
Allocation strategy : only satisfy the process's resource request when the resulting state is safe!
Algorithm for determining safe state The following data structures are required: int Available[NumResources];
/* Available[r]= number of free instances of resource r*/ int Max[NumProcs, NumResources];
/*Max[p,r]= maximum demand of process p for resource r*/ int Allocation[NumProcs, NumResources];
/* Allocation[p,r] = number of resources r actually allocated to p*/ int Need[NumProcs, NumResources];
/* Need[p,r] = Max[p,r] - Allocation[p,r]*/ 1. Suppose there are arrays
int Work[NumProcs, NumResources] = Available; int Finish[NumProcs] = false;
2. Find i such that Finish[i] == false Need[i] <= Work[i]
If there is no such i, go to step 4.
3. Work = Work + Allocation[i]; Finish[i] = true;
Go to step 2
4.If Finish[i] == true for all i, then the system is in a safe state. For example : Suppose the current state of the system is described as follows:
Max
Allocation | Available | |||||||
R1 | R2 | R3 | R1 | R2 | R3 | R1 | R2 | R3 |
P1 | 3 | 2 | 2 | 1 | 0 | 0 | ||
P2 | 6 | 1 | 3 | 2 | 1 | 1 | ||
P3 | 3 | 1 | 4 | 2 | 1 | 1 | ||
P4 | 4 | 2 | 2 | 0 | 0 | 2 | ||
Maybe you are interested!
-
 Unix - Linux operating system - Ha Quang Thuy, Nguyen Tri Thanh - 27
Unix - Linux operating system - Ha Quang Thuy, Nguyen Tri Thanh - 27 -
 Operating System Principles - 1
Operating System Principles - 1 -
 Cckt Shift In The Direction Of Industry, Operating System
Cckt Shift In The Direction Of Industry, Operating System -
 Car body electrical practice - 8
zt2i3t4l5ee
zt2a3gs
zt2a3ge
zc2o3n4t5e6n7ts
If the voltage is out of specification, replace the wire or connector.
If the voltage is within specification, install the front fog light relay and follow step 5.
Step 5 Check the front fog light switch
- Remove the D4 connector of the fog light switch
- Use a multimeter to measure the resistance of the front fog light switch.
Measurement location
Condition
Standard
D4-3 (BFG) -D4-4 (LFG)
Light switchFront Fog OFF
>10kΩ
D4-3 (BFG) -D4-4 (LFG)
Front fog light switchON
<1 Ω
- Standard resistor
D4 connector is located on the combination switch assembly.
If the resistance is out of specification, replace the combination switch (the fog light switch is located in the combination switch).
If the resistance is within specification, follow step 6.
Step 6 Check wiring and connectors (front fog light relay-light selector switch)
- Disconnect connector D4 of the combination switch assembly
- Use a voltmeter to measure the voltage value of jack D4 on the wire side.
Measurement location
Control modecontrol
Standard
D4-3 (BFG) - (-) AQ
TAIL
11 to 14 V
D4 connector for the wiring of the combination switch assembly
If the voltage does not meet the standard, replace the wire or connector.
If the voltage is within standard, there may have been an error in the previous measurements.
Step 7 Check the front fog lights
- Remove the front fog light electrical connector.
- Supply battery voltage to the fog lamp terminals
Jack 8, B9 of front fog lamp on the electrical side
blind first.
Power supply location
Terms and Conditions
Battery positive terminal - Terminal 2Battery negative terminal - Terminal 1
Fog lightsbefore morning
- If the light does not come on, replace the bulb.
If the light is on, re-plug the jack and continue to step 8.
Step 8 Check wiring and connectors (relay and front fog lights)
- Disconnect the B8 and B9 connectors of the front fog lights.
- Use a voltmeter to measure voltage at the following locations:
Measurement location
Switch location
Terms and Conditions
B8-2 - (-) AQ
Electric lock ON TAIL size switchFog switch ON
11 to 14 V
B9-2 - (-) AQ
Electric lock ONTAIL size switch Fog switch ON
11 to 14 V
B8 and B9 connectors on the front fog lamp wiring side
Voltage is not up to standard, repair or replace the jack. If up to standard, there may have been an error in the measurement process.
2.2.4. Procedure for removing, installing and adjusting fog lights 1. Procedure for removing
- Remove the front inner ear pads
Use a screwdriver to remove the 3 screws and remove the front part of the front inner ear liner
-Remove the fog light assembly
+ Disconnect the connector.
+ Use a screwdriver to remove 3 screws to remove the fog light cover
2. Installation sequence
-Rotate the fog lamp bulb in the direction indicated by the arrow as shown in the figure and remove the fog lamp from the fog lamp assembly.
-Rotate the fog light bulb in the direction indicated by the arrow as shown in the figure and install the light into the fog light assembly.
- Use a screwdriver to install the fog light cover
-Install the electrical connector
Attention: Be careful not to damage the plastic thread on the lamp assembly.
- Install the front inner ear pads
Use a screwdriver to install the front inner bumper with 3 screws.
3. Prepare the vehicle to adjust the fog light convergence. Prepare the vehicle:
- Make sure there is no damage or deformation to the vehicle body around the fog lights.
- Add fuel to the fuel tank
- Add oil to standard level.
- Add engine coolant to standard level.
- Inflate the tire to standard pressure.
- Place spare tire, tools and jack in original design position
- Do not leave any load in the luggage compartment.
- Let a person weighing about 75 kg sit in the driver's seat.
4. Prepare to check the fog light convergence
a/ Prepare the vehicle status as follows:
- Place the car in a dark enough place to see the lines. The lines are the dividing line, below which the light from the fog lights can be seen but above which it cannot.
- Place the car perpendicular to the wall.
- Keep a distance of 7.62 m between the center of the fog lamp and the wall.
- Park the car on level ground.
- Press the car down a few times to stabilize the suspension.
Note: A distance of approximately 7.62 m is required between the vehicle (fog lamp center) and the wall to adjust the convergence correctly. If the distance of 7.62 m cannot be achieved, set the correct distance of 3 m to check and adjust the fog lamp convergence. (Since the target area varies with the distance, please follow the instructions as shown in the figure.)
b/ Prepare a piece of thick white paper about 2 m high and 4 m wide to use as a screen.
c/ Draw a vertical line through the center of the screen (line V).
d/ Set the screen as shown in the picture. Note:
- Keep the screen perpendicular to the ground.
- Align the V line on the screen with the center of the vehicle.
e/Draw the reference lines (H, V LH and V RH lines) on the screen as shown in the figure.HINT:
Mark the center of the fog lamp on the screen. If the center mark cannot be seen on the fog lamp, use the center of the fog lamp or the manufacturer's name mark on the fog lamp as the center mark.
H line (fog light height):
Draw a line across the screen so that it passes through the center mark. Line H should be at the same height as the center mark of the fog light bulb.
Line V LH, V RH (center mark position of left fog lamp LH and right fog lamp RH):
Draw two lines so that they intersect line H at the center marks.
5. Check the fog light convergence
a/ Cover the fog lamp or remove the connector of the other side fog lamp to prevent light from the unchecked fog lamp from affecting the fog lamp convergence test.
b/ Start the engine.
c/ Turn on the fog lights and make sure that the dividing line is outside the standard area as shown in the drawing.
6. Adjust the fog light convergence
Use a screwdriver to adjust the fog light to the standard area by turning the toe adjustment screw.
Note: If the screw is adjusted too far, loosen it and then tighten it again, so that the last rotation of the light adjustment screw is clockwise.
3. Self-study questions
1. Describe the operating principle of the lighting system with automatic headlight function
2. Describe the operating principle of the lighting system with the function of rotating headlights when turning
3. Draw diagram and connect lighting system on Hyundai Porter car
4. Draw diagram and connect lighting system on Honda Accord 1992
5. Draw the lighting circuit on a 1993 Toyota Lexus
LESSON 3 MAINTENANCE AND REPAIR OF SIGNAL SYSTEM
I. IMPLEMENTATION GOAL
After completing this lesson, students will be able to:
- Distinguish between types of signals on cars
- Correctly describe common symptoms and suspected areas causing damage.
- Connecting signal circuits ensures technical requirements
- Disassemble, install, check, maintain and repair the signal system to ensure technical requirements.
- Ensure safety in work and industrial hygiene
II. LESSON CONTENT
1. General description
The signal system equipped on cars aims to create signals to notify other vehicles participating in traffic about the vehicle's operating status such as: stopping, parking, braking, reversing, turning...
Signals are used either by light such as headlamps, brake lights, turn signals….. or by sound such as horns, reverse music….
Just like the lighting system. A signal system circuit usually consists of: battery, fuse, wire, relay, electrical load and control switch. Only some switches of the signal system are on the combination switch. The switches of other signals are usually located in different locations such as in the gearbox or brake pedal……
2. Maintenance and repair
2.1. Turn signals and hazard lights
The installation location of the turn signal is shown in Figure 3.1. The turn signal control switch is located in the combination switch under the steering wheel. Turning this switch to the right or left will make the turn signal turn right or left.
The hazard light switch is used when the vehicle has a problem while participating in traffic. When the hazard light switch is turned on, all the turn signals on the vehicle will light up at a certain frequency. The hazard light switch is usually placed separately from the turn signal switch (some old cars integrate the hazard and turn signal switches on the same combination switch cluster).
Figure 3.1 Turn signal switch Figure 3.2 Hazard switch
The part that generates the flashing frequency for the lights is called a turn signal relay. The turn signal relay usually has 3 terminals: B (positive power supply); E (negative power supply); L (providing the turn signal switch to distribute to the
lamp)
2.1.1. Circuit diagram
To generate the frequency for the turn signal, a turn signal relay is used in the turn signal circuit. The current from the turn signal relay will be sent to the turn signal switch assembly to distribute the current to the turn signal lights for the driver's purpose.
Figure 3.3. Schematic diagram of a turn signal circuit without a hazard switch
1. Battery; 2. Electric lock; 3. Turn signal relay; 4. Turn signal switch; 5. Turn signal lamp; 6. Turn signal lamp; 7. Hazard switch
Figure 3.4 Schematic diagram of turn signal circuit with hazard switch
1. Battery; 2. Combination switch cluster; 3. Turn signal;
4. Turn signal light; 5. Turn signal relay
Today's cars no longer use three-pin turn signal relays (B, L, E) but use eight-pin turn signal relays (figure 3.5) (pin number 8 is used for hazard lights).
For this type, the current supplying the turn signal lights is supplied directly from the turn signal relay to the lights.
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent .s1 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s3 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; vertical-align: 1pt; } div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -9pt; } div.maincontent .s8 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s9 { color: #008000; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s10 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; te
Car body electrical practice - 8
zt2i3t4l5ee
zt2a3gs
zt2a3ge
zc2o3n4t5e6n7ts
If the voltage is out of specification, replace the wire or connector.
If the voltage is within specification, install the front fog light relay and follow step 5.
Step 5 Check the front fog light switch
- Remove the D4 connector of the fog light switch
- Use a multimeter to measure the resistance of the front fog light switch.
Measurement location
Condition
Standard
D4-3 (BFG) -D4-4 (LFG)
Light switchFront Fog OFF
>10kΩ
D4-3 (BFG) -D4-4 (LFG)
Front fog light switchON
<1 Ω
- Standard resistor
D4 connector is located on the combination switch assembly.
If the resistance is out of specification, replace the combination switch (the fog light switch is located in the combination switch).
If the resistance is within specification, follow step 6.
Step 6 Check wiring and connectors (front fog light relay-light selector switch)
- Disconnect connector D4 of the combination switch assembly
- Use a voltmeter to measure the voltage value of jack D4 on the wire side.
Measurement location
Control modecontrol
Standard
D4-3 (BFG) - (-) AQ
TAIL
11 to 14 V
D4 connector for the wiring of the combination switch assembly
If the voltage does not meet the standard, replace the wire or connector.
If the voltage is within standard, there may have been an error in the previous measurements.
Step 7 Check the front fog lights
- Remove the front fog light electrical connector.
- Supply battery voltage to the fog lamp terminals
Jack 8, B9 of front fog lamp on the electrical side
blind first.
Power supply location
Terms and Conditions
Battery positive terminal - Terminal 2Battery negative terminal - Terminal 1
Fog lightsbefore morning
- If the light does not come on, replace the bulb.
If the light is on, re-plug the jack and continue to step 8.
Step 8 Check wiring and connectors (relay and front fog lights)
- Disconnect the B8 and B9 connectors of the front fog lights.
- Use a voltmeter to measure voltage at the following locations:
Measurement location
Switch location
Terms and Conditions
B8-2 - (-) AQ
Electric lock ON TAIL size switchFog switch ON
11 to 14 V
B9-2 - (-) AQ
Electric lock ONTAIL size switch Fog switch ON
11 to 14 V
B8 and B9 connectors on the front fog lamp wiring side
Voltage is not up to standard, repair or replace the jack. If up to standard, there may have been an error in the measurement process.
2.2.4. Procedure for removing, installing and adjusting fog lights 1. Procedure for removing
- Remove the front inner ear pads
Use a screwdriver to remove the 3 screws and remove the front part of the front inner ear liner
-Remove the fog light assembly
+ Disconnect the connector.
+ Use a screwdriver to remove 3 screws to remove the fog light cover
2. Installation sequence
-Rotate the fog lamp bulb in the direction indicated by the arrow as shown in the figure and remove the fog lamp from the fog lamp assembly.
-Rotate the fog light bulb in the direction indicated by the arrow as shown in the figure and install the light into the fog light assembly.
- Use a screwdriver to install the fog light cover
-Install the electrical connector
Attention: Be careful not to damage the plastic thread on the lamp assembly.
- Install the front inner ear pads
Use a screwdriver to install the front inner bumper with 3 screws.
3. Prepare the vehicle to adjust the fog light convergence. Prepare the vehicle:
- Make sure there is no damage or deformation to the vehicle body around the fog lights.
- Add fuel to the fuel tank
- Add oil to standard level.
- Add engine coolant to standard level.
- Inflate the tire to standard pressure.
- Place spare tire, tools and jack in original design position
- Do not leave any load in the luggage compartment.
- Let a person weighing about 75 kg sit in the driver's seat.
4. Prepare to check the fog light convergence
a/ Prepare the vehicle status as follows:
- Place the car in a dark enough place to see the lines. The lines are the dividing line, below which the light from the fog lights can be seen but above which it cannot.
- Place the car perpendicular to the wall.
- Keep a distance of 7.62 m between the center of the fog lamp and the wall.
- Park the car on level ground.
- Press the car down a few times to stabilize the suspension.
Note: A distance of approximately 7.62 m is required between the vehicle (fog lamp center) and the wall to adjust the convergence correctly. If the distance of 7.62 m cannot be achieved, set the correct distance of 3 m to check and adjust the fog lamp convergence. (Since the target area varies with the distance, please follow the instructions as shown in the figure.)
b/ Prepare a piece of thick white paper about 2 m high and 4 m wide to use as a screen.
c/ Draw a vertical line through the center of the screen (line V).
d/ Set the screen as shown in the picture. Note:
- Keep the screen perpendicular to the ground.
- Align the V line on the screen with the center of the vehicle.
e/Draw the reference lines (H, V LH and V RH lines) on the screen as shown in the figure.HINT:
Mark the center of the fog lamp on the screen. If the center mark cannot be seen on the fog lamp, use the center of the fog lamp or the manufacturer's name mark on the fog lamp as the center mark.
H line (fog light height):
Draw a line across the screen so that it passes through the center mark. Line H should be at the same height as the center mark of the fog light bulb.
Line V LH, V RH (center mark position of left fog lamp LH and right fog lamp RH):
Draw two lines so that they intersect line H at the center marks.
5. Check the fog light convergence
a/ Cover the fog lamp or remove the connector of the other side fog lamp to prevent light from the unchecked fog lamp from affecting the fog lamp convergence test.
b/ Start the engine.
c/ Turn on the fog lights and make sure that the dividing line is outside the standard area as shown in the drawing.
6. Adjust the fog light convergence
Use a screwdriver to adjust the fog light to the standard area by turning the toe adjustment screw.
Note: If the screw is adjusted too far, loosen it and then tighten it again, so that the last rotation of the light adjustment screw is clockwise.
3. Self-study questions
1. Describe the operating principle of the lighting system with automatic headlight function
2. Describe the operating principle of the lighting system with the function of rotating headlights when turning
3. Draw diagram and connect lighting system on Hyundai Porter car
4. Draw diagram and connect lighting system on Honda Accord 1992
5. Draw the lighting circuit on a 1993 Toyota Lexus
LESSON 3 MAINTENANCE AND REPAIR OF SIGNAL SYSTEM
I. IMPLEMENTATION GOAL
After completing this lesson, students will be able to:
- Distinguish between types of signals on cars
- Correctly describe common symptoms and suspected areas causing damage.
- Connecting signal circuits ensures technical requirements
- Disassemble, install, check, maintain and repair the signal system to ensure technical requirements.
- Ensure safety in work and industrial hygiene
II. LESSON CONTENT
1. General description
The signal system equipped on cars aims to create signals to notify other vehicles participating in traffic about the vehicle's operating status such as: stopping, parking, braking, reversing, turning...
Signals are used either by light such as headlamps, brake lights, turn signals….. or by sound such as horns, reverse music….
Just like the lighting system. A signal system circuit usually consists of: battery, fuse, wire, relay, electrical load and control switch. Only some switches of the signal system are on the combination switch. The switches of other signals are usually located in different locations such as in the gearbox or brake pedal……
2. Maintenance and repair
2.1. Turn signals and hazard lights
The installation location of the turn signal is shown in Figure 3.1. The turn signal control switch is located in the combination switch under the steering wheel. Turning this switch to the right or left will make the turn signal turn right or left.
The hazard light switch is used when the vehicle has a problem while participating in traffic. When the hazard light switch is turned on, all the turn signals on the vehicle will light up at a certain frequency. The hazard light switch is usually placed separately from the turn signal switch (some old cars integrate the hazard and turn signal switches on the same combination switch cluster).
Figure 3.1 Turn signal switch Figure 3.2 Hazard switch
The part that generates the flashing frequency for the lights is called a turn signal relay. The turn signal relay usually has 3 terminals: B (positive power supply); E (negative power supply); L (providing the turn signal switch to distribute to the
lamp)
2.1.1. Circuit diagram
To generate the frequency for the turn signal, a turn signal relay is used in the turn signal circuit. The current from the turn signal relay will be sent to the turn signal switch assembly to distribute the current to the turn signal lights for the driver's purpose.
Figure 3.3. Schematic diagram of a turn signal circuit without a hazard switch
1. Battery; 2. Electric lock; 3. Turn signal relay; 4. Turn signal switch; 5. Turn signal lamp; 6. Turn signal lamp; 7. Hazard switch
Figure 3.4 Schematic diagram of turn signal circuit with hazard switch
1. Battery; 2. Combination switch cluster; 3. Turn signal;
4. Turn signal light; 5. Turn signal relay
Today's cars no longer use three-pin turn signal relays (B, L, E) but use eight-pin turn signal relays (figure 3.5) (pin number 8 is used for hazard lights).
For this type, the current supplying the turn signal lights is supplied directly from the turn signal relay to the lights.
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; } div.maincontent .s1 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s3 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; } div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; vertical-align: 1pt; } div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; vertical-align: -9pt; } div.maincontent .s8 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; } div.maincontent .s9 { color: #008000; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; } div.maincontent .s10 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; te -
![Pre-tax Profit of Bidv Tien Giang in the Period 2011-2015
zt2i3t4l5ee
zt2a3gsnon-credit services, joint stock commercial bank
zt2a3ge
zc2o3n4t5e6n7ts
At that time, the Branch had to set aside a provision for credit risks, which reduced the Branchs income.
Chart 2.2. Pre-tax profit of BIDV Tien Giang in the period 2011-2015
Unit: Billion VND
140
120
100
80
60
40
20
0
63.3
80.34
89.29
110.08
131.99
2011 2012 2013 2014 2015
Profit before tax
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, through chart 2.2, it can be seen that BIDV Tien Giangs profit is still increasing continuously, and its operating efficiency is currently leaking. This is a contribution of non-credit services, and this service segment will be increasingly focused on growth by BIDV Tien Giang to ensure the highest profit safety because credit activities have many potential risks. At the same time, focusing on developing non-credit services is consistent with one of the contents of restructuring the financial activities of credit institutions in the project Restructuring the system of credit institutions in the period 2011-2015 approved by the Prime Minister in Decision No. 254/QD-TTg dated March 1, 2012 [14]: Gradually shifting the business model of commercial banks towards reducing dependence on credit activities and increasing income from non-credit services.
2.2. Current status of non-credit service development at BIDV Tien Giang.
2.2.1. BIDV Tien Giang has deployed the development of non-credit services in recent times.
Along with the development of the Head Office, BIDV Tien Giangs products and services are constantly improved and deployed in a diverse manner to ensure provision for many different customer groups in the area: individual customers, corporate customers, and financial institutions. Typical services are as follows: Payment services, treasury services, guarantee services, card services, trade finance, other services: Western Union, insurance commissions, consulting services, foreign exchange derivatives trading, e-banking services,...
2.2.1.1. Payment services:
In accordance with the Prime Ministers Project to promote non-cash payments in Vietnam [15], banks in Tien Giang province have continuously developed payment services to reduce customers cash usage habits through card services and electronic banking services such as: salary payment through accounts, focusing on developing card acceptance points, developing multi-purpose cards, paying social insurance by transfer, paying bills through banks, etc.
Chart 2.3. Net income from payment services in the period 2011-2015
Unit: Million VND
6000
5000
4000
3000
2000
1000
0
3922 4065
4720 5084 5324
2011 2012 2013 2014 2015
Net income from payment services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Along with the technological development of the entire system, BIDV Tien Giang has a payment system with a fairly stable transaction processing speed, bringing many conveniences to customers. The results of observing chart 2.3 show that the income from payment services that the Branch has achieved has grown over the years but the speed is not high and the products are not outstanding compared to other banks. Domestic payment products such as: Online bill payment, electricity bills, water bills, insurance premiums, cable TV bills, telecommunications fees, airline tickets, etc. bring many conveniences to customers. Regarding international payment, this is an indispensable activity for foreign economic activities, BIDV Tien Giang is providing international payment methods for small enterprises producing agriculture, aquatic food and seafood that have credit relationships with banks in industrial parks in Tien Giang province such as: money transfer, collection, L/C payment.
2.2.1.2. Treasury services:
BIDV Tien Giang always focuses on ensuring treasury safety and currency security, always complies with legal regulations, and minimizes risks in operations such as: counting and collecting money from customers, receiving and delivering internal transactions, collecting from the State Bank (SBV) or other credit institutions, receiving ATM funds, bundling money, etc. BIDV Tien Giangs treasury service management department is always fully equipped with modern machinery and equipment such as: money transport vehicles, fire prevention tools, money counters, money detectors, magnifying glasses, etc. to ensure absolute safety in treasury operations, immediately identifying real and fake money and other risks that may affect people and assets of the bank and customers. In addition, implementing regulation 2480/QC dated October 28, 2008 between the State Bank of Tien Giang province and the Provincial Police on coordination in the fight against counterfeit money, in the 3-year review of implementation, BIDV Tien Giang discovered, seized and submitted to the State Bank of Tien Giang province 475 banknotes of various denominations and was commended by the Provincial Police and the State Bank of Tien Giang province [17].
Chart 2.4. Net income from treasury services in the period 2011-2015
Unit: Million VND
350
300
250
200
150
100
50
0
105 122
309 289 279
2011 2012 2013 2014 2015
Net income from treasury services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, as shown in Figure 2.4, income from treasury operations is not high and fluctuates. Specifically, in the period 2011-2013, net income increased and increased most sharply in 2013, then in the period 2013-2015, there was a downward trend. This fluctuation is due to the fact that fees collected from treasury services are often very low and can even be waived to attract customers to use other services.
2.2.1.3. Guarantee and trade finance services:
BIDV Tien Giang, thanks to the advantages of the province and the favorable location of the Branch, has continuously focused on developing income from guarantee services and trade finance.
Chart 2.5. Net income from guarantee and trade finance services in the period 2011-2015
Unit: Million VND
14000
12000
10000
8000
6000
4000
2000
0
5193 5695
2742 3420
8889
3992
11604 12206
5143 5312
2011 2012 2013 2014 2015
Net income from guarantee services Net income from Trade Finance
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.5, we can see that BIDV Tien Giangs income from guarantee services and trade finance has grown over the years. The reason is: Among BIDV Tien Giangs corporate customers, the construction industry is the industry with the highest proportion of customers after the trading industry, this is a group of customers with potential to develop guarantee services. The second group of customers is corporate customers in the fields of agricultural production, livestock and seafood processing with high import and export turnover in the area.
are the target of trade finance development. In addition, BIDV Tien Giang also focuses on continuously developing these customer groups to increase revenue for many other products and services in the future.
2.2.1.4. Card and POS services:
As a service that BIDV Tien Giang has recently developed strongly, it can be said that this is a very potential market and has the ability to develop even more strongly in the future. Card services with outstanding advantages such as fast payment time, wide payment range, quite safe, effective and suitable for the integration trend and the Project to promote non-cash payments in Vietnam. Cards have become a modern and popular payment tool. BIDV Tien Giang early identified that developing card services is to expand the market to people in society, create capital mobilized from card-opened accounts, contribute to diversifying banking activities, enhance the image of the bank, bring the BIDV Tien Giang brand to people as quickly and easily as possible. BIDV Tien Giang is currently providing card types such as: credit cards (BIDV MasterCard Platinum, BIDV Visa Gold Precious, BIDV Visa Manchester United, BIDV Visa Classic), international debit cards (BIDV Ready Card, BIDV Manu Debit Card), domestic debit cards (BIDV Harmony Card, BIDV eTrans Card, BIDV Moving Card, BIDV-Lingo Co-branded Card, BIDV-Co.opmart Co-branded Card). These cards can be paid via POS/EDC or on the ATM system. In addition, with debit cards, customers can not only withdraw money via ATMs but also perform utilities such as mobile top-up, online payment, money transfer,... through electronic banking services.
In order to attract customers with card services, BIDV Tien Giang has continuously increased the installation of ATMs. As of December 31, 2015, BIDV Tien Giang has 23 ATMs combined with 7 ATMs in the same system of BIDV My Tho, so the number of ATMs is quite large, especially in the center of My Tho City, but is not yet fully present in the districts. Basic services on ATMs such as withdrawing money, checking balances, printing short statements,... BIDV ATMs accept cards from banks in the system.
Banknetvn and Smartlink, cards branded by international card organizations Union Pay (CUP), VISA, MasterCard and cards of banks in the Asian Payment Network. From here, cardholders can make bill payments for themselves or others at ATMs, by simply entering the subscriber number or customer code, booking code that service providers notify and make bill payments.
Chart 2.6. Net income from card services in the period 2011-2015
Unit: Million VND
3500
3000
2500
2000
1500
1000
500
0
687
1023
1547
2267
3104
2011 2012 2013 2014 2015
Net income from card services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.6, it can be seen that BIDV Tien Giangs card service income is constantly growing because the Branch focuses on developing businesses operating in industrial parks, which are the source of customers for salary payment products, ATMs, BSMS. Specifically, there are companies such as Freeview, Quang Viet, Dai Thanh, which are businesses with a large number of card openings at the Branch, contributing to the increase in card service fees [25].
Table 2.6. Number of ATMs and POS machines in 2015 of some banks in Tien Giang area.
Unit: Machine
STT
Bank name
Number of ATMs
Cumulative number of ATM cards
POS machine
1
BIDV Tien Giang
23
97,095
22
2
BIDV My Tho
7
21,325
0
3
Agribank Tien Giang
29
115,743
77
4
Vietinbank Tien Giang
16
100,052
54
5
Dong A Tien Giang
26
97,536
11
6
Sacombank Tien Giang
24
88,513
27
7
Vietcombank Tien Giang
15
61,607
96
8
Vietinbank - Tay Tien Giang Branch
6
46,042
38
(Source: 2015 Banking Activity Data Report of the General and Internal Control Department of the Provincial State Bank [21])
Through table 2.6, the author finds that the number of ATMs of BIDV Tien Giang is not much, ranking fourth after Agribank Tien Giang, Dong A Tien Giang, Sacombank Tien Giang. The number of POS machines of BIDV Tien Giang is very small, only higher than Dong A Tien Giang and BIDV My Tho in the initial stages of merging the BIDV system. Besides, BIDV Tien Giang has a high number of cards increasing over the years (table 2.7) but the cumulative number of cards issued up to December 31, 2015 is still relatively low compared to Agribank, Vietcombank, Dong A (table 2.6).
div.maincontent .content_head3 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .p { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent p { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent .s1 { color: black; font-family:Courier New, monospace; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s2 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s3 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s4 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s5 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s6 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s7 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13.5pt; }
div.maincontent .s8 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; }
div.maincontent .s9 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -2pt; }
div.maincontent .s10 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; }
div.maincontent .s11 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -5pt; }
div.maincontent .s12 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -3pt; }
div.maincontent .s13 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -4pt; }
div.maincontent .s14 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 7.5pt; }
div.maincontent .s15 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s16 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s17 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9.5pt; }
div.maincontent .s18 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s19 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s20 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -2pt; }
div.maincontent .s21 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10pt; }
div.maincontent .s22 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s23 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -3pt; }
div.maincontent .s24 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s25 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s26 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s27 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -6pt; }
div.maincontent .s28 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s29 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s30 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s31 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s32 { color: black; font-family:.VnTime, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s33 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s34 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s35 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s36 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s37 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 13pt; }
div.maincontent .s38 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s39 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 15pt; }
div.maincontent .s40 { color: black; font-family:Times New Roman, serif; font-style: normal; fo](data:image/svg+xml,%3Csvg%20xmlns=%22http://www.w3.org/2000/svg%22%20viewBox=%220%200%2075%2075%22%3E%3C/svg%3E) Pre-tax Profit of Bidv Tien Giang in the Period 2011-2015
zt2i3t4l5ee
zt2a3gsnon-credit services, joint stock commercial bank
zt2a3ge
zc2o3n4t5e6n7ts
At that time, the Branch had to set aside a provision for credit risks, which reduced the Branch's income.
Chart 2.2. Pre-tax profit of BIDV Tien Giang in the period 2011-2015
Unit: Billion VND
140
120
100
80
60
40
20
0
63.3
80.34
89.29
110.08
131.99
2011 2012 2013 2014 2015
Profit before tax
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, through chart 2.2, it can be seen that BIDV Tien Giang's profit is still increasing continuously, and its operating efficiency is currently leaking. This is a contribution of non-credit services, and this service segment will be increasingly focused on growth by BIDV Tien Giang to ensure the highest profit safety because credit activities have many potential risks. At the same time, focusing on developing non-credit services is consistent with one of the contents of restructuring the financial activities of credit institutions in the project "Restructuring the system of credit institutions in the period 2011-2015" approved by the Prime Minister in Decision No. 254/QD-TTg dated March 1, 2012 [14]: "Gradually shifting the business model of commercial banks towards reducing dependence on credit activities and increasing income from non-credit services".
2.2. Current status of non-credit service development at BIDV Tien Giang.
2.2.1. BIDV Tien Giang has deployed the development of non-credit services in recent times.
Along with the development of the Head Office, BIDV Tien Giang's products and services are constantly improved and deployed in a diverse manner to ensure provision for many different customer groups in the area: individual customers, corporate customers, and financial institutions. Typical services are as follows: Payment services, treasury services, guarantee services, card services, trade finance, other services: Western Union, insurance commissions, consulting services, foreign exchange derivatives trading, e-banking services,...
2.2.1.1. Payment services:
In accordance with the Prime Minister's Project to promote non-cash payments in Vietnam [15], banks in Tien Giang province have continuously developed payment services to reduce customers' cash usage habits through card services and electronic banking services such as: salary payment through accounts, focusing on developing card acceptance points, developing multi-purpose cards, paying social insurance by transfer, paying bills through banks, etc.
Chart 2.3. Net income from payment services in the period 2011-2015
Unit: Million VND
6000
5000
4000
3000
2000
1000
0
3922 4065
4720 5084 5324
2011 2012 2013 2014 2015
Net income from payment services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Along with the technological development of the entire system, BIDV Tien Giang has a payment system with a fairly stable transaction processing speed, bringing many conveniences to customers. The results of observing chart 2.3 show that the income from payment services that the Branch has achieved has grown over the years but the speed is not high and the products are not outstanding compared to other banks. Domestic payment products such as: Online bill payment, electricity bills, water bills, insurance premiums, cable TV bills, telecommunications fees, airline tickets, etc. bring many conveniences to customers. Regarding international payment, this is an indispensable activity for foreign economic activities, BIDV Tien Giang is providing international payment methods for small enterprises producing agriculture, aquatic food and seafood that have credit relationships with banks in industrial parks in Tien Giang province such as: money transfer, collection, L/C payment.
2.2.1.2. Treasury services:
BIDV Tien Giang always focuses on ensuring treasury safety and currency security, always complies with legal regulations, and minimizes risks in operations such as: counting and collecting money from customers, receiving and delivering internal transactions, collecting from the State Bank (SBV) or other credit institutions, receiving ATM funds, bundling money, etc. BIDV Tien Giang's treasury service management department is always fully equipped with modern machinery and equipment such as: money transport vehicles, fire prevention tools, money counters, money detectors, magnifying glasses, etc. to ensure absolute safety in treasury operations, immediately identifying real and fake money and other risks that may affect people and assets of the bank and customers. In addition, implementing regulation 2480/QC dated October 28, 2008 between the State Bank of Tien Giang province and the Provincial Police on coordination in the fight against counterfeit money, in the 3-year review of implementation, BIDV Tien Giang discovered, seized and submitted to the State Bank of Tien Giang province 475 banknotes of various denominations and was commended by the Provincial Police and the State Bank of Tien Giang province [17].
Chart 2.4. Net income from treasury services in the period 2011-2015
Unit: Million VND
350
300
250
200
150
100
50
0
105 122
309 289 279
2011 2012 2013 2014 2015
Net income from treasury services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, as shown in Figure 2.4, income from treasury operations is not high and fluctuates. Specifically, in the period 2011-2013, net income increased and increased most sharply in 2013, then in the period 2013-2015, there was a downward trend. This fluctuation is due to the fact that fees collected from treasury services are often very low and can even be waived to attract customers to use other services.
2.2.1.3. Guarantee and trade finance services:
BIDV Tien Giang, thanks to the advantages of the province and the favorable location of the Branch, has continuously focused on developing income from guarantee services and trade finance.
Chart 2.5. Net income from guarantee and trade finance services in the period 2011-2015
Unit: Million VND
14000
12000
10000
8000
6000
4000
2000
0
5193 5695
2742 3420
8889
3992
11604 12206
5143 5312
2011 2012 2013 2014 2015
Net income from guarantee services Net income from Trade Finance
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.5, we can see that BIDV Tien Giang's income from guarantee services and trade finance has grown over the years. The reason is: Among BIDV Tien Giang's corporate customers, the construction industry is the industry with the highest proportion of customers after the trading industry, this is a group of customers with potential to develop guarantee services. The second group of customers is corporate customers in the fields of agricultural production, livestock and seafood processing with high import and export turnover in the area.
are the target of trade finance development. In addition, BIDV Tien Giang also focuses on continuously developing these customer groups to increase revenue for many other products and services in the future.
2.2.1.4. Card and POS services:
As a service that BIDV Tien Giang has recently developed strongly, it can be said that this is a very potential market and has the ability to develop even more strongly in the future. Card services with outstanding advantages such as fast payment time, wide payment range, quite safe, effective and suitable for the integration trend and the Project to promote non-cash payments in Vietnam. Cards have become a modern and popular payment tool. BIDV Tien Giang early identified that developing card services is to expand the market to people in society, create capital mobilized from card-opened accounts, contribute to diversifying banking activities, enhance the image of the bank, bring the BIDV Tien Giang brand to people as quickly and easily as possible. BIDV Tien Giang is currently providing card types such as: credit cards (BIDV MasterCard Platinum, BIDV Visa Gold Precious, BIDV Visa Manchester United, BIDV Visa Classic), international debit cards (BIDV Ready Card, BIDV Manu Debit Card), domestic debit cards (BIDV Harmony Card, BIDV eTrans Card, BIDV Moving Card, BIDV-Lingo Co-branded Card, BIDV-Co.opmart Co-branded Card). These cards can be paid via POS/EDC or on the ATM system. In addition, with debit cards, customers can not only withdraw money via ATMs but also perform utilities such as mobile top-up, online payment, money transfer,... through electronic banking services.
In order to attract customers with card services, BIDV Tien Giang has continuously increased the installation of ATMs. As of December 31, 2015, BIDV Tien Giang has 23 ATMs combined with 7 ATMs in the same system of BIDV My Tho, so the number of ATMs is quite large, especially in the center of My Tho City, but is not yet fully present in the districts. Basic services on ATMs such as withdrawing money, checking balances, printing short statements,... BIDV ATMs accept cards from banks in the system.
Banknetvn and Smartlink, cards branded by international card organizations Union Pay (CUP), VISA, MasterCard and cards of banks in the Asian Payment Network. From here, cardholders can make bill payments for themselves or others at ATMs, by simply entering the subscriber number or customer code, booking code that service providers notify and make bill payments.
Chart 2.6. Net income from card services in the period 2011-2015
Unit: Million VND
3500
3000
2500
2000
1500
1000
500
0
687
1023
1547
2267
3104
2011 2012 2013 2014 2015
Net income from card services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.6, it can be seen that BIDV Tien Giang's card service income is constantly growing because the Branch focuses on developing businesses operating in industrial parks, which are the source of customers for salary payment products, ATMs, BSMS. Specifically, there are companies such as Freeview, Quang Viet, Dai Thanh, which are businesses with a large number of card openings at the Branch, contributing to the increase in card service fees [25].
Table 2.6. Number of ATMs and POS machines in 2015 of some banks in Tien Giang area.
Unit: Machine
STT
Bank name
Number of ATMs
Cumulative number of ATM cards
POS machine
1
BIDV Tien Giang
23
97,095
22
2
BIDV My Tho
7
21,325
0
3
Agribank Tien Giang
29
115,743
77
4
Vietinbank Tien Giang
16
100,052
54
5
Dong A Tien Giang
26
97,536
11
6
Sacombank Tien Giang
24
88,513
27
7
Vietcombank Tien Giang
15
61,607
96
8
Vietinbank - Tay Tien Giang Branch
6
46,042
38
(Source: 2015 Banking Activity Data Report of the General and Internal Control Department of the Provincial State Bank [21])
Through table 2.6, the author finds that the number of ATMs of BIDV Tien Giang is not much, ranking fourth after Agribank Tien Giang, Dong A Tien Giang, Sacombank Tien Giang. The number of POS machines of BIDV Tien Giang is very small, only higher than Dong A Tien Giang and BIDV My Tho in the initial stages of merging the BIDV system. Besides, BIDV Tien Giang has a high number of cards increasing over the years (table 2.7) but the cumulative number of cards issued up to December 31, 2015 is still relatively low compared to Agribank, Vietcombank, Dong A (table 2.6).
div.maincontent .content_head3 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent .s1 { color: black; font-family:"Courier New", monospace; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s3 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13.5pt; }
div.maincontent .s8 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; }
div.maincontent .s9 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -2pt; }
div.maincontent .s10 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; }
div.maincontent .s11 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -5pt; }
div.maincontent .s12 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -3pt; }
div.maincontent .s13 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -4pt; }
div.maincontent .s14 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 7.5pt; }
div.maincontent .s15 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s16 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s17 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9.5pt; }
div.maincontent .s18 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s19 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s20 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -2pt; }
div.maincontent .s21 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10pt; }
div.maincontent .s22 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s23 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -3pt; }
div.maincontent .s24 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s25 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s26 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s27 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -6pt; }
div.maincontent .s28 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s29 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s30 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s31 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s32 { color: black; font-family:.VnTime, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s33 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s34 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s35 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s36 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s37 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 13pt; }
div.maincontent .s38 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s39 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 15pt; }
div.maincontent .s40 { color: black; font-family:"Times New Roman", serif; font-style: normal; fo
Pre-tax Profit of Bidv Tien Giang in the Period 2011-2015
zt2i3t4l5ee
zt2a3gsnon-credit services, joint stock commercial bank
zt2a3ge
zc2o3n4t5e6n7ts
At that time, the Branch had to set aside a provision for credit risks, which reduced the Branch's income.
Chart 2.2. Pre-tax profit of BIDV Tien Giang in the period 2011-2015
Unit: Billion VND
140
120
100
80
60
40
20
0
63.3
80.34
89.29
110.08
131.99
2011 2012 2013 2014 2015
Profit before tax
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, through chart 2.2, it can be seen that BIDV Tien Giang's profit is still increasing continuously, and its operating efficiency is currently leaking. This is a contribution of non-credit services, and this service segment will be increasingly focused on growth by BIDV Tien Giang to ensure the highest profit safety because credit activities have many potential risks. At the same time, focusing on developing non-credit services is consistent with one of the contents of restructuring the financial activities of credit institutions in the project "Restructuring the system of credit institutions in the period 2011-2015" approved by the Prime Minister in Decision No. 254/QD-TTg dated March 1, 2012 [14]: "Gradually shifting the business model of commercial banks towards reducing dependence on credit activities and increasing income from non-credit services".
2.2. Current status of non-credit service development at BIDV Tien Giang.
2.2.1. BIDV Tien Giang has deployed the development of non-credit services in recent times.
Along with the development of the Head Office, BIDV Tien Giang's products and services are constantly improved and deployed in a diverse manner to ensure provision for many different customer groups in the area: individual customers, corporate customers, and financial institutions. Typical services are as follows: Payment services, treasury services, guarantee services, card services, trade finance, other services: Western Union, insurance commissions, consulting services, foreign exchange derivatives trading, e-banking services,...
2.2.1.1. Payment services:
In accordance with the Prime Minister's Project to promote non-cash payments in Vietnam [15], banks in Tien Giang province have continuously developed payment services to reduce customers' cash usage habits through card services and electronic banking services such as: salary payment through accounts, focusing on developing card acceptance points, developing multi-purpose cards, paying social insurance by transfer, paying bills through banks, etc.
Chart 2.3. Net income from payment services in the period 2011-2015
Unit: Million VND
6000
5000
4000
3000
2000
1000
0
3922 4065
4720 5084 5324
2011 2012 2013 2014 2015
Net income from payment services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Along with the technological development of the entire system, BIDV Tien Giang has a payment system with a fairly stable transaction processing speed, bringing many conveniences to customers. The results of observing chart 2.3 show that the income from payment services that the Branch has achieved has grown over the years but the speed is not high and the products are not outstanding compared to other banks. Domestic payment products such as: Online bill payment, electricity bills, water bills, insurance premiums, cable TV bills, telecommunications fees, airline tickets, etc. bring many conveniences to customers. Regarding international payment, this is an indispensable activity for foreign economic activities, BIDV Tien Giang is providing international payment methods for small enterprises producing agriculture, aquatic food and seafood that have credit relationships with banks in industrial parks in Tien Giang province such as: money transfer, collection, L/C payment.
2.2.1.2. Treasury services:
BIDV Tien Giang always focuses on ensuring treasury safety and currency security, always complies with legal regulations, and minimizes risks in operations such as: counting and collecting money from customers, receiving and delivering internal transactions, collecting from the State Bank (SBV) or other credit institutions, receiving ATM funds, bundling money, etc. BIDV Tien Giang's treasury service management department is always fully equipped with modern machinery and equipment such as: money transport vehicles, fire prevention tools, money counters, money detectors, magnifying glasses, etc. to ensure absolute safety in treasury operations, immediately identifying real and fake money and other risks that may affect people and assets of the bank and customers. In addition, implementing regulation 2480/QC dated October 28, 2008 between the State Bank of Tien Giang province and the Provincial Police on coordination in the fight against counterfeit money, in the 3-year review of implementation, BIDV Tien Giang discovered, seized and submitted to the State Bank of Tien Giang province 475 banknotes of various denominations and was commended by the Provincial Police and the State Bank of Tien Giang province [17].
Chart 2.4. Net income from treasury services in the period 2011-2015
Unit: Million VND
350
300
250
200
150
100
50
0
105 122
309 289 279
2011 2012 2013 2014 2015
Net income from treasury services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, as shown in Figure 2.4, income from treasury operations is not high and fluctuates. Specifically, in the period 2011-2013, net income increased and increased most sharply in 2013, then in the period 2013-2015, there was a downward trend. This fluctuation is due to the fact that fees collected from treasury services are often very low and can even be waived to attract customers to use other services.
2.2.1.3. Guarantee and trade finance services:
BIDV Tien Giang, thanks to the advantages of the province and the favorable location of the Branch, has continuously focused on developing income from guarantee services and trade finance.
Chart 2.5. Net income from guarantee and trade finance services in the period 2011-2015
Unit: Million VND
14000
12000
10000
8000
6000
4000
2000
0
5193 5695
2742 3420
8889
3992
11604 12206
5143 5312
2011 2012 2013 2014 2015
Net income from guarantee services Net income from Trade Finance
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.5, we can see that BIDV Tien Giang's income from guarantee services and trade finance has grown over the years. The reason is: Among BIDV Tien Giang's corporate customers, the construction industry is the industry with the highest proportion of customers after the trading industry, this is a group of customers with potential to develop guarantee services. The second group of customers is corporate customers in the fields of agricultural production, livestock and seafood processing with high import and export turnover in the area.
are the target of trade finance development. In addition, BIDV Tien Giang also focuses on continuously developing these customer groups to increase revenue for many other products and services in the future.
2.2.1.4. Card and POS services:
As a service that BIDV Tien Giang has recently developed strongly, it can be said that this is a very potential market and has the ability to develop even more strongly in the future. Card services with outstanding advantages such as fast payment time, wide payment range, quite safe, effective and suitable for the integration trend and the Project to promote non-cash payments in Vietnam. Cards have become a modern and popular payment tool. BIDV Tien Giang early identified that developing card services is to expand the market to people in society, create capital mobilized from card-opened accounts, contribute to diversifying banking activities, enhance the image of the bank, bring the BIDV Tien Giang brand to people as quickly and easily as possible. BIDV Tien Giang is currently providing card types such as: credit cards (BIDV MasterCard Platinum, BIDV Visa Gold Precious, BIDV Visa Manchester United, BIDV Visa Classic), international debit cards (BIDV Ready Card, BIDV Manu Debit Card), domestic debit cards (BIDV Harmony Card, BIDV eTrans Card, BIDV Moving Card, BIDV-Lingo Co-branded Card, BIDV-Co.opmart Co-branded Card). These cards can be paid via POS/EDC or on the ATM system. In addition, with debit cards, customers can not only withdraw money via ATMs but also perform utilities such as mobile top-up, online payment, money transfer,... through electronic banking services.
In order to attract customers with card services, BIDV Tien Giang has continuously increased the installation of ATMs. As of December 31, 2015, BIDV Tien Giang has 23 ATMs combined with 7 ATMs in the same system of BIDV My Tho, so the number of ATMs is quite large, especially in the center of My Tho City, but is not yet fully present in the districts. Basic services on ATMs such as withdrawing money, checking balances, printing short statements,... BIDV ATMs accept cards from banks in the system.
Banknetvn and Smartlink, cards branded by international card organizations Union Pay (CUP), VISA, MasterCard and cards of banks in the Asian Payment Network. From here, cardholders can make bill payments for themselves or others at ATMs, by simply entering the subscriber number or customer code, booking code that service providers notify and make bill payments.
Chart 2.6. Net income from card services in the period 2011-2015
Unit: Million VND
3500
3000
2500
2000
1500
1000
500
0
687
1023
1547
2267
3104
2011 2012 2013 2014 2015
Net income from card services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.6, it can be seen that BIDV Tien Giang's card service income is constantly growing because the Branch focuses on developing businesses operating in industrial parks, which are the source of customers for salary payment products, ATMs, BSMS. Specifically, there are companies such as Freeview, Quang Viet, Dai Thanh, which are businesses with a large number of card openings at the Branch, contributing to the increase in card service fees [25].
Table 2.6. Number of ATMs and POS machines in 2015 of some banks in Tien Giang area.
Unit: Machine
STT
Bank name
Number of ATMs
Cumulative number of ATM cards
POS machine
1
BIDV Tien Giang
23
97,095
22
2
BIDV My Tho
7
21,325
0
3
Agribank Tien Giang
29
115,743
77
4
Vietinbank Tien Giang
16
100,052
54
5
Dong A Tien Giang
26
97,536
11
6
Sacombank Tien Giang
24
88,513
27
7
Vietcombank Tien Giang
15
61,607
96
8
Vietinbank - Tay Tien Giang Branch
6
46,042
38
(Source: 2015 Banking Activity Data Report of the General and Internal Control Department of the Provincial State Bank [21])
Through table 2.6, the author finds that the number of ATMs of BIDV Tien Giang is not much, ranking fourth after Agribank Tien Giang, Dong A Tien Giang, Sacombank Tien Giang. The number of POS machines of BIDV Tien Giang is very small, only higher than Dong A Tien Giang and BIDV My Tho in the initial stages of merging the BIDV system. Besides, BIDV Tien Giang has a high number of cards increasing over the years (table 2.7) but the cumulative number of cards issued up to December 31, 2015 is still relatively low compared to Agribank, Vietcombank, Dong A (table 2.6).
div.maincontent .content_head3 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent p { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent .s1 { color: black; font-family:"Courier New", monospace; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s2 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s3 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s4 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s5 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s6 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s7 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13.5pt; }
div.maincontent .s8 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; }
div.maincontent .s9 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -2pt; }
div.maincontent .s10 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; }
div.maincontent .s11 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -5pt; }
div.maincontent .s12 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -3pt; }
div.maincontent .s13 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -4pt; }
div.maincontent .s14 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 7.5pt; }
div.maincontent .s15 { color: black; font-family:"Times New Roman", serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s16 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s17 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9.5pt; }
div.maincontent .s18 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s19 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s20 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -2pt; }
div.maincontent .s21 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10pt; }
div.maincontent .s22 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s23 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -3pt; }
div.maincontent .s24 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s25 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s26 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s27 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -6pt; }
div.maincontent .s28 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s29 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s30 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s31 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s32 { color: black; font-family:.VnTime, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s33 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s34 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s35 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s36 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s37 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 13pt; }
div.maincontent .s38 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s39 { color: black; font-family:"Times New Roman", serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 15pt; }
div.maincontent .s40 { color: black; font-family:"Times New Roman", serif; font-style: normal; fo
If process P2 requests 4 for R1, 1 for R3. Can this request be met without causing a deadlock? Seeing that Available[1] =4, Available[3] =2 is enough to satisfy P2's request, we have
Need
Allocation | Available | |||||||
R1 | R2 | R3 | R1 | R2 | R3 | R1 | R2 | R3 |
P1 | 2 | 2 | 2 | 1 | 0 | 0 | ||
P2 | 0 | 0 | 1 | 6 | 1 | 2 | ||
P3 | 1 | 0 | 3 | 2 | 1 | 1 | ||
P4 | 4 | 2 | 0 | 0 | 0 | 2 | ||
Need
Allocation | Available | |||||||
R1 | R2 | R3 | R1 | R2 | R3 | R1 | R2 | R3 |
P1 | 2 | 2 | 2 | 1 | 0 | 0 | ||
P2 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P3 | 1 | 0 | 3 | 2 | 1 | 1 | ||
P4 | 4 | 2 | 0 | 0 | 0 | 2 | ||
Need
Allocation | Available | |||||||
R1 | R2 | R3 | R1 | R2 | R3 | R1 | R2 | R3 |
0 | 0 | 0 | 0 | 0 | 0 | |||
P2 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P3 | 1 | 0 | 3 | 2 | 1 | 1 | ||
P4 | 4 | 2 | 0 | 0 | 0 | 2 |
P1
Need
Allocation | Available | |||||||
R1 | R2 | R3 | R1 | R2 | R3 | R1 | R2 | R3 |
P1 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P2 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P3 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P4 | 4 | 2 | 0 | 0 | 0 | 2 | ||
Need
Allocation | Available | |||||||
R1 | R2 | R3 | R1 | R2 | R3 | R1 | R2 | R3 |
P1 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P2 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P3 | 0 | 0 | 0 | 0 | 0 | 0 | ||
P4 | 0 | 0 | 0 | 0 | 0 | 0 | ||
The resulting state is safe and allocable. The algorithm requires resources.
Suppose process Pi requests k instances of resource r .
1.If k <= Need[i], go to step 2 Otherwise, an error occurs 2.If k <= Available[i], go to step 3 Otherwise, Pi must wait
3. Suppose the system has allocated Pi the resources it requested and updated the system status as follows:
Available[i] = Available[i] - k; Allocation[i]= Allocation[i]+ k; Need[i] = Need[i] - k;
If the resulting state is safe, the above resources will now be actually allocated to Pi.
On the contrary, Pi has to wait
Detect blockages
The following data structures are required: int Available[NumResources];
// Available[r]= number of free instances of resource r int Allocation[NumProcs, NumResources];
// Allocation[p,r] = number of resources r actually allocated to p int Request[NumProcs, NumResources];
// Request[p,r] = number of resources r that process p requests Congestion Detection Algorithm
1. int Work[NumResources] = Available; int Finish[NumProcs];
for (i = 0; i < NumProcs; i++) Finish[i] = (Allocation[i] == 0);
2. Find i such that Finish[i] == false Request[i] <= Work
If there is no such i, go to step 4.
3. Work = Work + Allocation[i]; Finish[i] = true;
Go to step 2
4. If Finish[i] == true for all i, then the system is deadlock free.
If Finish[i] == false for some value i,
then processes for which Finish[i] == false will be in deadlock.
Correcting congestion
Once a deadlock is detected, there are two main options for correcting the deadlock: Suspend the execution of the involved processes
This approach is based on reclaiming resources of terminated processes. One of the following two methods can be used:
-Suspend all processes in a deadlocked state
-Suspend each related process until there is no more deadlock cycle: to choose the appropriate process to be suspended, it is necessary to rely on factors such as priority, processing time, number of resources occupied, number of resources requested...
Resource Recovery
Deadlock can be corrected by preempting some resources from processes and allocating these resources to other processes until the deadlock cycle is eliminated. Three problems need to be solved:
-Choosing a victim: which process will have its resources revoked? and which resources will be revoked?
-Revert to pre-deadlock state: when reclaiming resources of a process, it is necessary to restore the state of the process back to the most recent previous state without deadlock.
-The "resource starvation" situation: how to ensure that no process is always deprived of resources?
Memory Management
This lesson will help you visualize the issues that need to be considered when designing the memory management module of the Operating System. Some memory organization models are also introduced and analyzed their advantages and disadvantages so that you can understand how memory allocation and recovery takes place.
Main memory is the only storage device through which the CPU can exchange information with the external environment, so the need to organize and manage memory is one of the top priorities of the operating system. Main memory is organized as a one-dimensional array of memory words, each memory word has an address. Information exchange with the external environment is done through reading or writing data to a specific address in memory.
Most modern operating systems allow multitasking to improve CPU utilization. However, this technique creates the need to share memory between different processes. The problem is that: « memory is finite and memory requirements are infinite ».
The operating system is responsible for allocating memory to processes that request it. To perform this task well, the operating system needs to consider many aspects:
Address correspondencelogical and physical addresses( physical ) : how to convert a symbolic address in the program to a real address in main memory?
Physical memory management : how to expand available memory to host multiple concurrent processes?
Information sharing : how to allow two processes to share information in memory?
Protection : How to prevent processes from invading memory allocated to other processes?
Memory management solutions are highly dependent on hardware characteristics and have gone through many stages of improvement to become the quite satisfactory solutions they are today.




![Pre-tax Profit of Bidv Tien Giang in the Period 2011-2015
zt2i3t4l5ee
zt2a3gsnon-credit services, joint stock commercial bank
zt2a3ge
zc2o3n4t5e6n7ts
At that time, the Branch had to set aside a provision for credit risks, which reduced the Branchs income.
Chart 2.2. Pre-tax profit of BIDV Tien Giang in the period 2011-2015
Unit: Billion VND
140
120
100
80
60
40
20
0
63.3
80.34
89.29
110.08
131.99
2011 2012 2013 2014 2015
Profit before tax
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, through chart 2.2, it can be seen that BIDV Tien Giangs profit is still increasing continuously, and its operating efficiency is currently leaking. This is a contribution of non-credit services, and this service segment will be increasingly focused on growth by BIDV Tien Giang to ensure the highest profit safety because credit activities have many potential risks. At the same time, focusing on developing non-credit services is consistent with one of the contents of restructuring the financial activities of credit institutions in the project Restructuring the system of credit institutions in the period 2011-2015 approved by the Prime Minister in Decision No. 254/QD-TTg dated March 1, 2012 [14]: Gradually shifting the business model of commercial banks towards reducing dependence on credit activities and increasing income from non-credit services.
2.2. Current status of non-credit service development at BIDV Tien Giang.
2.2.1. BIDV Tien Giang has deployed the development of non-credit services in recent times.
Along with the development of the Head Office, BIDV Tien Giangs products and services are constantly improved and deployed in a diverse manner to ensure provision for many different customer groups in the area: individual customers, corporate customers, and financial institutions. Typical services are as follows: Payment services, treasury services, guarantee services, card services, trade finance, other services: Western Union, insurance commissions, consulting services, foreign exchange derivatives trading, e-banking services,...
2.2.1.1. Payment services:
In accordance with the Prime Ministers Project to promote non-cash payments in Vietnam [15], banks in Tien Giang province have continuously developed payment services to reduce customers cash usage habits through card services and electronic banking services such as: salary payment through accounts, focusing on developing card acceptance points, developing multi-purpose cards, paying social insurance by transfer, paying bills through banks, etc.
Chart 2.3. Net income from payment services in the period 2011-2015
Unit: Million VND
6000
5000
4000
3000
2000
1000
0
3922 4065
4720 5084 5324
2011 2012 2013 2014 2015
Net income from payment services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Along with the technological development of the entire system, BIDV Tien Giang has a payment system with a fairly stable transaction processing speed, bringing many conveniences to customers. The results of observing chart 2.3 show that the income from payment services that the Branch has achieved has grown over the years but the speed is not high and the products are not outstanding compared to other banks. Domestic payment products such as: Online bill payment, electricity bills, water bills, insurance premiums, cable TV bills, telecommunications fees, airline tickets, etc. bring many conveniences to customers. Regarding international payment, this is an indispensable activity for foreign economic activities, BIDV Tien Giang is providing international payment methods for small enterprises producing agriculture, aquatic food and seafood that have credit relationships with banks in industrial parks in Tien Giang province such as: money transfer, collection, L/C payment.
2.2.1.2. Treasury services:
BIDV Tien Giang always focuses on ensuring treasury safety and currency security, always complies with legal regulations, and minimizes risks in operations such as: counting and collecting money from customers, receiving and delivering internal transactions, collecting from the State Bank (SBV) or other credit institutions, receiving ATM funds, bundling money, etc. BIDV Tien Giangs treasury service management department is always fully equipped with modern machinery and equipment such as: money transport vehicles, fire prevention tools, money counters, money detectors, magnifying glasses, etc. to ensure absolute safety in treasury operations, immediately identifying real and fake money and other risks that may affect people and assets of the bank and customers. In addition, implementing regulation 2480/QC dated October 28, 2008 between the State Bank of Tien Giang province and the Provincial Police on coordination in the fight against counterfeit money, in the 3-year review of implementation, BIDV Tien Giang discovered, seized and submitted to the State Bank of Tien Giang province 475 banknotes of various denominations and was commended by the Provincial Police and the State Bank of Tien Giang province [17].
Chart 2.4. Net income from treasury services in the period 2011-2015
Unit: Million VND
350
300
250
200
150
100
50
0
105 122
309 289 279
2011 2012 2013 2014 2015
Net income from treasury services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
However, as shown in Figure 2.4, income from treasury operations is not high and fluctuates. Specifically, in the period 2011-2013, net income increased and increased most sharply in 2013, then in the period 2013-2015, there was a downward trend. This fluctuation is due to the fact that fees collected from treasury services are often very low and can even be waived to attract customers to use other services.
2.2.1.3. Guarantee and trade finance services:
BIDV Tien Giang, thanks to the advantages of the province and the favorable location of the Branch, has continuously focused on developing income from guarantee services and trade finance.
Chart 2.5. Net income from guarantee and trade finance services in the period 2011-2015
Unit: Million VND
14000
12000
10000
8000
6000
4000
2000
0
5193 5695
2742 3420
8889
3992
11604 12206
5143 5312
2011 2012 2013 2014 2015
Net income from guarantee services Net income from Trade Finance
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.5, we can see that BIDV Tien Giangs income from guarantee services and trade finance has grown over the years. The reason is: Among BIDV Tien Giangs corporate customers, the construction industry is the industry with the highest proportion of customers after the trading industry, this is a group of customers with potential to develop guarantee services. The second group of customers is corporate customers in the fields of agricultural production, livestock and seafood processing with high import and export turnover in the area.
are the target of trade finance development. In addition, BIDV Tien Giang also focuses on continuously developing these customer groups to increase revenue for many other products and services in the future.
2.2.1.4. Card and POS services:
As a service that BIDV Tien Giang has recently developed strongly, it can be said that this is a very potential market and has the ability to develop even more strongly in the future. Card services with outstanding advantages such as fast payment time, wide payment range, quite safe, effective and suitable for the integration trend and the Project to promote non-cash payments in Vietnam. Cards have become a modern and popular payment tool. BIDV Tien Giang early identified that developing card services is to expand the market to people in society, create capital mobilized from card-opened accounts, contribute to diversifying banking activities, enhance the image of the bank, bring the BIDV Tien Giang brand to people as quickly and easily as possible. BIDV Tien Giang is currently providing card types such as: credit cards (BIDV MasterCard Platinum, BIDV Visa Gold Precious, BIDV Visa Manchester United, BIDV Visa Classic), international debit cards (BIDV Ready Card, BIDV Manu Debit Card), domestic debit cards (BIDV Harmony Card, BIDV eTrans Card, BIDV Moving Card, BIDV-Lingo Co-branded Card, BIDV-Co.opmart Co-branded Card). These cards can be paid via POS/EDC or on the ATM system. In addition, with debit cards, customers can not only withdraw money via ATMs but also perform utilities such as mobile top-up, online payment, money transfer,... through electronic banking services.
In order to attract customers with card services, BIDV Tien Giang has continuously increased the installation of ATMs. As of December 31, 2015, BIDV Tien Giang has 23 ATMs combined with 7 ATMs in the same system of BIDV My Tho, so the number of ATMs is quite large, especially in the center of My Tho City, but is not yet fully present in the districts. Basic services on ATMs such as withdrawing money, checking balances, printing short statements,... BIDV ATMs accept cards from banks in the system.
Banknetvn and Smartlink, cards branded by international card organizations Union Pay (CUP), VISA, MasterCard and cards of banks in the Asian Payment Network. From here, cardholders can make bill payments for themselves or others at ATMs, by simply entering the subscriber number or customer code, booking code that service providers notify and make bill payments.
Chart 2.6. Net income from card services in the period 2011-2015
Unit: Million VND
3500
3000
2500
2000
1500
1000
500
0
687
1023
1547
2267
3104
2011 2012 2013 2014 2015
Net income from card services
(Source: Report on the implementation of the annual business plan of the General Planning Department of BIDV Tien Giang [24])
Through chart 2.6, it can be seen that BIDV Tien Giangs card service income is constantly growing because the Branch focuses on developing businesses operating in industrial parks, which are the source of customers for salary payment products, ATMs, BSMS. Specifically, there are companies such as Freeview, Quang Viet, Dai Thanh, which are businesses with a large number of card openings at the Branch, contributing to the increase in card service fees [25].
Table 2.6. Number of ATMs and POS machines in 2015 of some banks in Tien Giang area.
Unit: Machine
STT
Bank name
Number of ATMs
Cumulative number of ATM cards
POS machine
1
BIDV Tien Giang
23
97,095
22
2
BIDV My Tho
7
21,325
0
3
Agribank Tien Giang
29
115,743
77
4
Vietinbank Tien Giang
16
100,052
54
5
Dong A Tien Giang
26
97,536
11
6
Sacombank Tien Giang
24
88,513
27
7
Vietcombank Tien Giang
15
61,607
96
8
Vietinbank - Tay Tien Giang Branch
6
46,042
38
(Source: 2015 Banking Activity Data Report of the General and Internal Control Department of the Provincial State Bank [21])
Through table 2.6, the author finds that the number of ATMs of BIDV Tien Giang is not much, ranking fourth after Agribank Tien Giang, Dong A Tien Giang, Sacombank Tien Giang. The number of POS machines of BIDV Tien Giang is very small, only higher than Dong A Tien Giang and BIDV My Tho in the initial stages of merging the BIDV system. Besides, BIDV Tien Giang has a high number of cards increasing over the years (table 2.7) but the cumulative number of cards issued up to December 31, 2015 is still relatively low compared to Agribank, Vietcombank, Dong A (table 2.6).
div.maincontent .content_head3 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .p { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent p { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; margin:0pt; }
div.maincontent .s1 { color: black; font-family:Courier New, monospace; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s2 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s3 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s4 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s5 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s6 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s7 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13.5pt; }
div.maincontent .s8 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; }
div.maincontent .s9 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -2pt; }
div.maincontent .s10 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: 5pt; }
div.maincontent .s11 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -5pt; }
div.maincontent .s12 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -3pt; }
div.maincontent .s13 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9pt; vertical-align: -4pt; }
div.maincontent .s14 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 7.5pt; }
div.maincontent .s15 { color: black; font-family:Times New Roman, serif; font-style: italic; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s16 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s17 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 9.5pt; }
div.maincontent .s18 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s19 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s20 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -2pt; }
div.maincontent .s21 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10pt; }
div.maincontent .s22 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s23 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -3pt; }
div.maincontent .s24 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -5pt; }
div.maincontent .s25 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s26 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s27 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -6pt; }
div.maincontent .s28 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -1pt; }
div.maincontent .s29 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s30 { color: black; font-family:Calibri, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s31 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11pt; }
div.maincontent .s32 { color: black; font-family:.VnTime, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 14pt; }
div.maincontent .s33 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; }
div.maincontent .s34 { color: black; font-family:Cambria, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 10.5pt; vertical-align: -4pt; }
div.maincontent .s35 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 11.5pt; }
div.maincontent .s36 { color: black; font-family:Arial, sans-serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 14pt; }
div.maincontent .s37 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: bold; text-decoration: none; font-size: 13pt; }
div.maincontent .s38 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 13pt; }
div.maincontent .s39 { color: black; font-family:Times New Roman, serif; font-style: normal; font-weight: normal; text-decoration: none; font-size: 15pt; }
div.maincontent .s40 { color: black; font-family:Times New Roman, serif; font-style: normal; fo](https://tailieuthamkhao.com/uploads/2022/06/06/dich-vu-phi-tin-dung-tai-ngan-hang-thuong-mai-co-phan-dau-tu-va-phat-8-1-120x90.png)