- Availability: Will cloud services unexpectedly crash, leaving users unable to access their services and data for periods of time, affecting their work?
- Data loss: Some cloud storage services suddenly stop working or stop providing services, forcing users to back up their data from the “cloud” to their personal computers. This will take a lot of time. In some cases, for some reason, users' data is lost and cannot be recovered.
- Data portability and ownership: the question is, can users share data from one cloud service to another? Or in case they do not want to continue using the service provided from the cloud, can users back up all their data from the cloud? And how can users be sure that the cloud services will not destroy all their data in case the service is down.
- Security: The problem of data concentration on clouds is an effective way to enhance security, but on the other hand, it is also a concern for users of cloud computing services. Because once the clouds are attacked or broken into, all data will be occupied. However, this is not really a problem specific to cloud computing, because data theft attacks are a problem encountered in any environment, even on personal computers.
- Users are dependent on the technology and service quality of the provider, which reduces their flexibility and creativity. Users are only allowed to do things within the scope of the administrator's permission. Moreover, the latest information is often not updated promptly by the network operator, while customers want to keep up with the latest improvements. Therefore, customers feel unsatisfied, even frustrated by that control, or due to errors, network congestion...
Maybe you are interested!
-
 Research and deployment of private cloud computing using Hyper-V - 1
Research and deployment of private cloud computing using Hyper-V - 1 -
 Some Key Solutions to Promote Positive Changes and Limit Negative Changes of Socialist Production Relations in
Some Key Solutions to Promote Positive Changes and Limit Negative Changes of Socialist Production Relations in -
 Some solutions to limit risks in international goods trading activities of Vietnamese traders - 10
Some solutions to limit risks in international goods trading activities of Vietnamese traders - 10 -
 Solutions for developing competitive strategies of Vietnam Airlines - 2
Solutions for developing competitive strategies of Vietnam Airlines - 2 -
 Some Solutions to Improve the Legal System of Alimony
Some Solutions to Improve the Legal System of Alimony
1.6 Cloud computing deployment models
The word “cloud” originated from the illustration of the Internet and has been widely used in drawings of computer network systems in the information technology world. In simple terms, cloud computing is the Internet computing model. However, as the cloud computing model gradually takes shape, its advantages have been applied to
in environments of different sizes and scopes, forming different deployment models.
1.6.1 Public clouds
The first model mentioned when referring to Cloud Computing is the Public Cloud model. This is a model in which the Cloud Computing infrastructure is owned by an organization and provides services to customers widely through the Internet or wide area public networks. Different applications share the same computing, network and storage resources. Therefore, the Cloud Computing infrastructure is designed to ensure data isolation between customers and separate access.
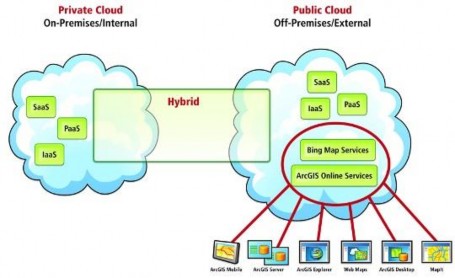
Figure 1.5: Illustration of a public cloud
Public Cloud services are aimed at a large number of customers, so they often have high infrastructure capacity, meet flexible computing needs, and bring low costs to customers. Therefore, customers of services on Public Cloud will include all classes, where individual customers and small businesses will have the advantage of easy access to high-tech, quality applications without initial investment, low cost of use, and flexibility.
1.6.2 Private Cloud
Private Cloud is a cloud service that is owned by an enterprise and served to its users. Private Cloud can be operated by a third party and the cloud infrastructure can be located inside or outside the owning organization (at a third party operator or even a fourth party).
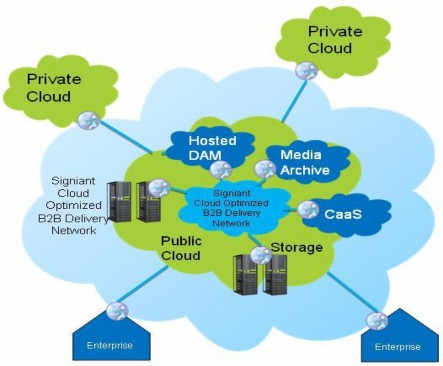
Figure 1.6: Illustration of a private cloud
Private Cloud is built by large organizations and enterprises to exploit the technological advantages and management capabilities of Cloud Computing. With Private Cloud, enterprises optimize their IT infrastructure, improve efficiency in using and managing resources allocation and recovery, thereby reducing the time to bring products to market.
1.6.3 Hybrid Clouds
Hybrid Cloud is a combination of public and private clouds. These private clouds are typically created by the enterprise and management responsibilities are divided between the enterprise and the public cloud provider.
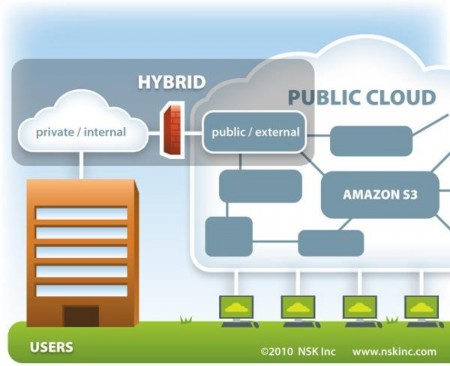
Figure 1.7: Illustration of a hybrid cloud
1.6.4 Community Cloud
Community Cloud is a cloud shared by an organization and supports a specific community with common interests (e.g. common mission, security requirements, policies…). It can be managed by the organization or a third party.
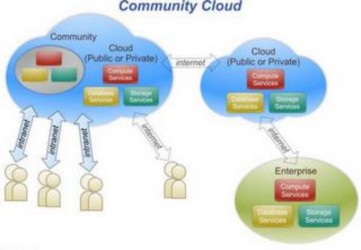
Figure 1.8: Illustration of a public cloud
1.7 Cloud Computing Problem Solutions
The advent of cloud computing has solved the following problems:
1.7.1 Data storage issues
Data is stored centrally in giant data warehouses. Large companies like Microsoft and Google have dozens of central data warehouses scattered around the world.
These large companies will provide services that allow businesses to store and manage their data on central repositories.
1.7.2 The problem of computing power
Imagine your laptop or phone as a workstation, then the cloud is the server that manages all those workstations, stores data and can process for the workstations. The workstations will have their own data but most of it is constantly synchronized with the server in a seamless connection. For example, if you change the calendar application on your phone, the calendar application is immediately synchronized to the computer in real time. In general, in cloud computing, software will become a service to serve the user.
User data is stored on virtual servers in the cloud to be processed on it. Because the processing speed of the server is very high, all operations will be processed faster and work more smoothly, if you have a strong connection to keep them connected. Of course, because the workstations do not need to process anymore, they do not need to be too powerful, reducing costs for users.
1.7.3 Resource and software provision issues
Providing services such as IAAS (infrastructure as a service), PAAS (Platform as a service), SAAS (Software as a service).
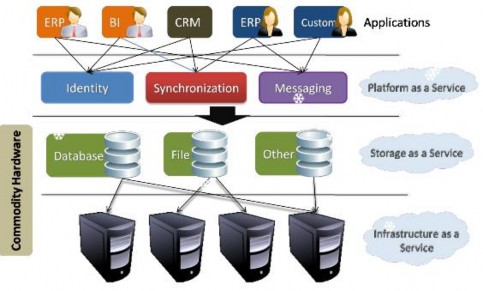
Figure 1.9: Illustration of services
1.8 Security in cloud computing
1.8.1 Cloud information security objectives
- Security: protection against attacks
- Confidentiality: Protect data from being viewed by others.
- Availability: Applications provided on cloud computing are always available. Quickly recover when problems occur. Provide long-term services. Have data insurance if the service provider stops working.
1.8.2 Security solutions for cloud computing deployment systems
1.8.2.1 Management
Manages and oversees policies, procedures, and standards for application development as well as the design, implementation, testing, and monitoring of service deployment.
1.8.2.2 Comply with data security regulations
Compliance refers to conformance to specifications, standards, regulations, or laws. Different forms of security and privacy laws and regulations exist within different countries. Creating a common regulation that is suitable everywhere is a difficult problem for cloud service providers and cloud computing environments.
1.8.2.3 Trust
Under the cloud computing model, an organization must give up direct management of the security and safety aspects of its information and data. This means that it has brought a very high level of trust to the cloud computing service provider.
1.8.2.4 System architecture
The architecture of the software systems used to provide cloud services consists of the hardware and software that reside in the clouds. The physical location of the infrastructure is defined by the cloud service provider as a logical representation of reliability and scalability. Virtual machines often serve as an abstraction of the deployment units and are also relatively loosely coupled to the cloud storage architecture. Applications are built on top of the programming interface of the Internet access service, which often involves multiple cloud components communicating with each other via application programming interfaces.
1.8.2.5 Identification and access management
Security of sensitive information and data is increasingly becoming a concern for organizations. Unauthorized access to information resources in the cloud is a major concern for most customers using cloud computing services. A common concern is the identification and authentication of the organization's scope. That scope may not naturally extend in the cloud and extending or modifying existing frameworks to support cloud services can be difficult. The choice of using two different authentication systems, one for internal organizational systems and one for external systems via the cloud platform is a form of confusion and may become unfeasible in the future. Identity, widely disseminated with the advent of service-oriented architectures, is a solution that can be achieved in a number of ways such as the Security Assertion Markup Language (SAML) standard or the OpenID standard.
1.8.2.6 Isolation of software systems
To achieve the desired high scale of consumption, cloud service providers ensure the provision of service elasticity and resource isolation of subscribers. Many components in cloud computing are often deployed by combining multiple virtual machines of users with different needs on the same physical server. It is important to note that applications deployed on virtualized clients are still very vulnerable to attacks and threats.
1.8.2.7 Data protection
Data stored in the cloud often resides in an environment shared with other customers. Organizations that transfer sensitive data and modify that data in the cloud must therefore ensure that accounts for accessing the data are tightly controlled and that the data is stored securely.
1.8.2.8 Be prepared to deal with possible incidents
Availability is the degree to which an organization's full set of computing resources are accessible and usable. Availability can be affected temporarily or permanently. Denial of service attacks, equipment outages, and natural disasters are all threats. Downtime is often difficult to control and can impact the work of individuals or organizations using the service.
1.8.2.9 Responding to incidents
Incident response is an organizational approach to dealing with the consequences of an attack on computer systems. The role of cloud service providers is very important in performing incident response activities. Including troubleshooting, analyzing attacks, verifying incidents, collecting data, etc.
1.9 Current status of cloud computing applications in Vietnam
Not outside the general trend of the world's information technology industry, when the use of cloud computing services is becoming more and more popular in countries with developed information technology. Vietnam is gradually approaching cloud services through projects of some foreign enterprises such as Microsoft, Intel, ... This technology is considered a solution to the problems that many companies are facing such as lack of information technology capacity, limited investment costs ... Most information technology leaders are quite hopeful when commenting on this technology.
Vietnam is one of the first countries in ASEAN to use cloud computing. Cloud computing in Vietnam began to show positive signs when FPT - Vietnam's leading technology company affirmed its pioneering position in technology by signing a cooperation agreement with Microsoft Asia - Trend Micro to develop "cloud" in Asia. FPT then continued to cooperate with Microsoft in May 2010. The focus of this cooperation is an agreement to develop a cloud computing platform based on Microsoft technology. Both parties are aiming to develop a platform for cloud services including collaborative communications, data storage and infrastructure services, to serve the needs of a large number of customers. FPT IS provides a number of cloud-based applications such as Office 365 services (including Exchange Online providing e-mail, calendar, and contact services; SharePoint Online supporting users to collaborate with social networking features via the Internet; Integrated Office Web Apps, helping to edit Microsoft Office documents online...). FPT Telecom applies cloud computing technology to deploy Fshare file sharing service according to the "public cloud" model, allowing users to store and send files according to the motto "anytime, anywhere" as well as providing a type of back-end storage for third-party services.
Misa is also an information technology enterprise with network investments in deploying applications based on cloud computing platforms. With products